For Healthcare
Secure external assets from attacks targeting healthcare systems and patient data.
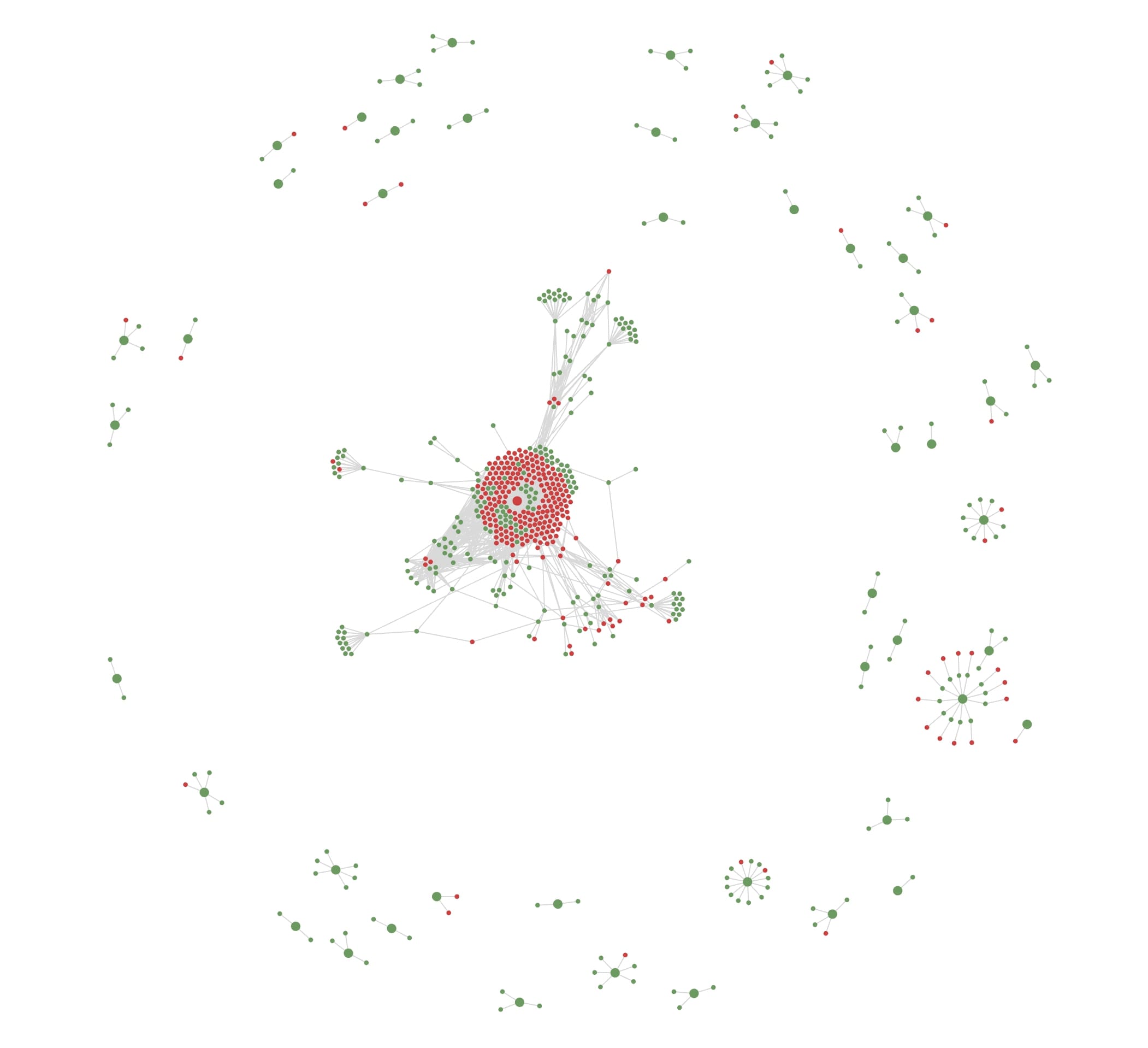
Uncover all public-facing assets
Identify and catalog all assets behind connected medical systems and remote services.
Tackle security issues that can disrupt patient care
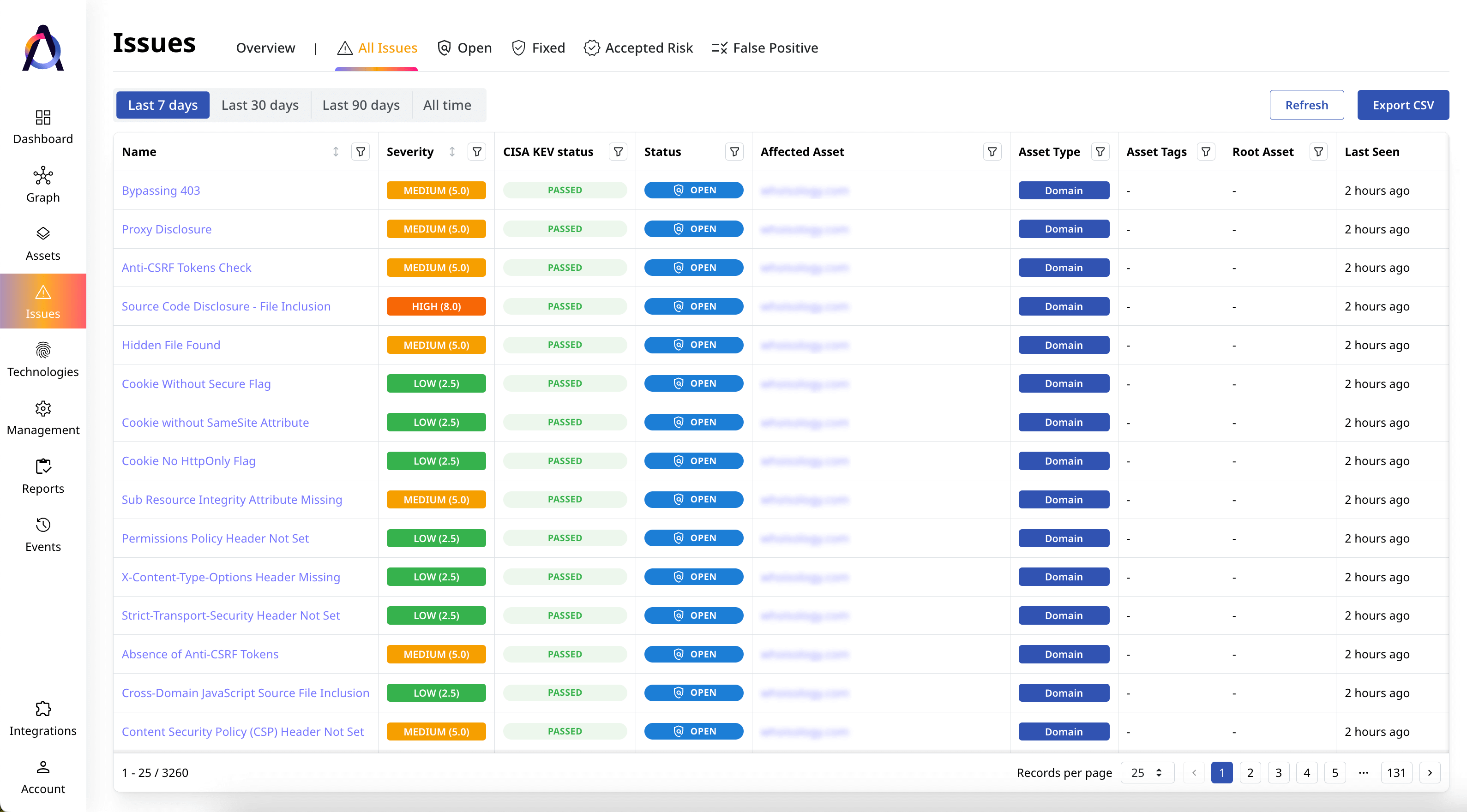
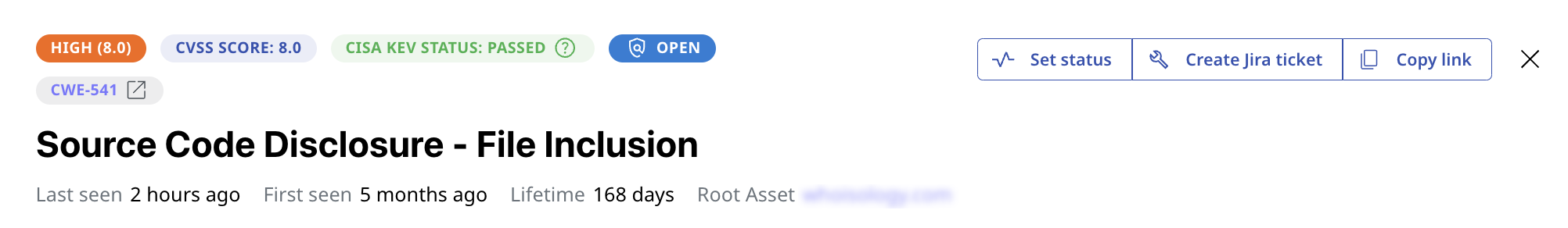
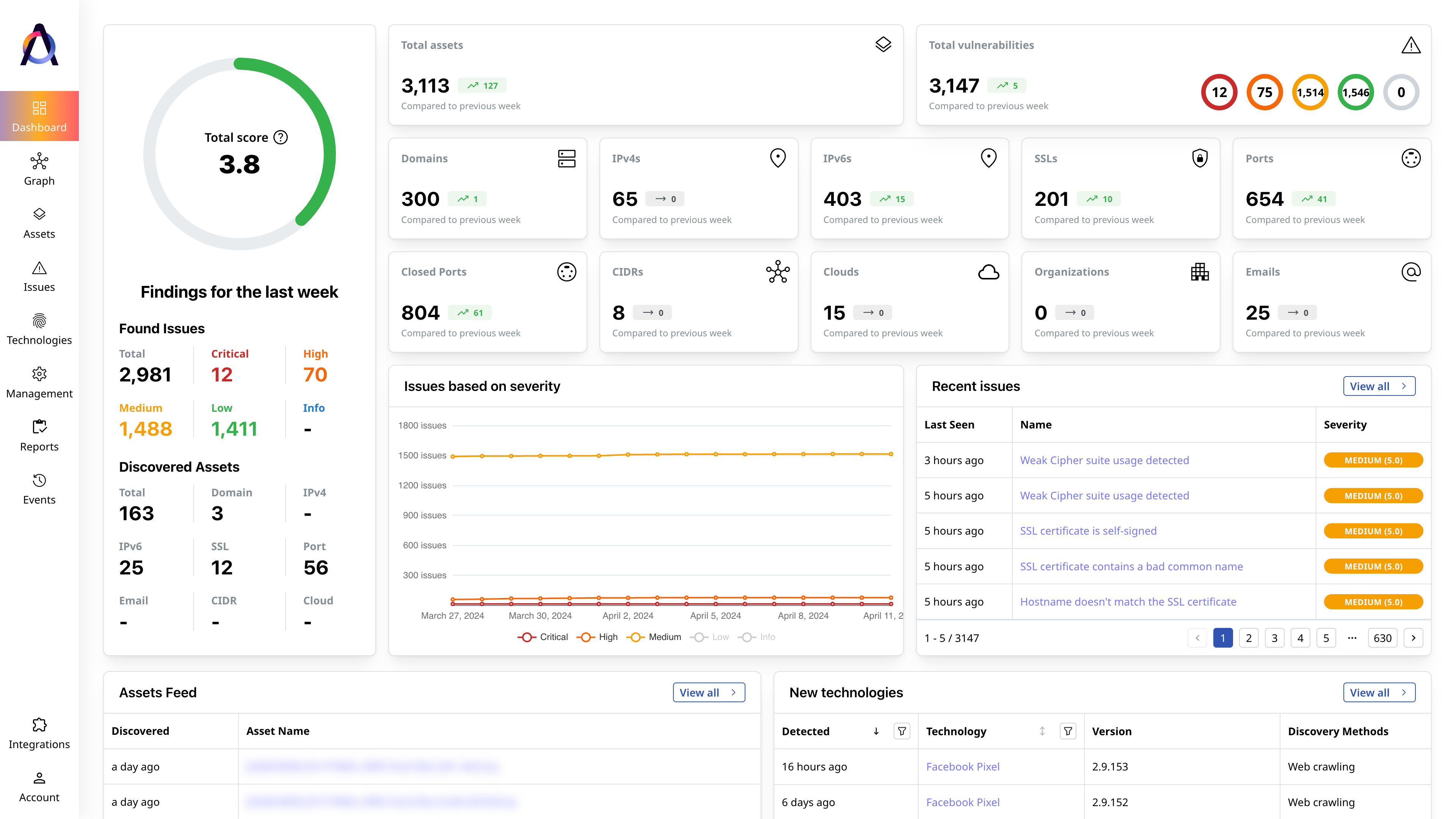
Detect security gaps in your public-facing infrastructure and evaluate them based on their severity and relevance.
Protect connected healthcare systems
Continuously find new assets and emerging security risks to minimize exposure to disruptive cyber attacks.
-
Superior Coverage
Uncover twice as many assets across web-facing systems and networks.
-
Complete Inventory
Access comprehensive catalogs of exposed assets and their issues.
-
C-Level Reporting
Assess your security posture at a glance and drill down on each issue.
What security experts say
Featured Resources

How Are Attack Vectors and Attack Surfaces Related?
Attack vectors and attack surfaces are deeply intertwined cybersecurity concepts. In a nutshell, an attack surface is the sum of all attack vectors in[...]

CWE Vs. CVE Vs. CVSS: What Are the Differences?
When protecting your digital infrastructure from threats, it’s critical to become familiar with security standards like CWE, CVE, and CVSS. These term[...]

How to Find Vulnerabilities in a Website
Website vulnerabilities are exploitable weaknesses that allow attackers to access data without authorization, steal sensitive information, or disrupt[...]