For Entertainment
Protect external assets to prevent business interruption, IP theft, and PII leaks.
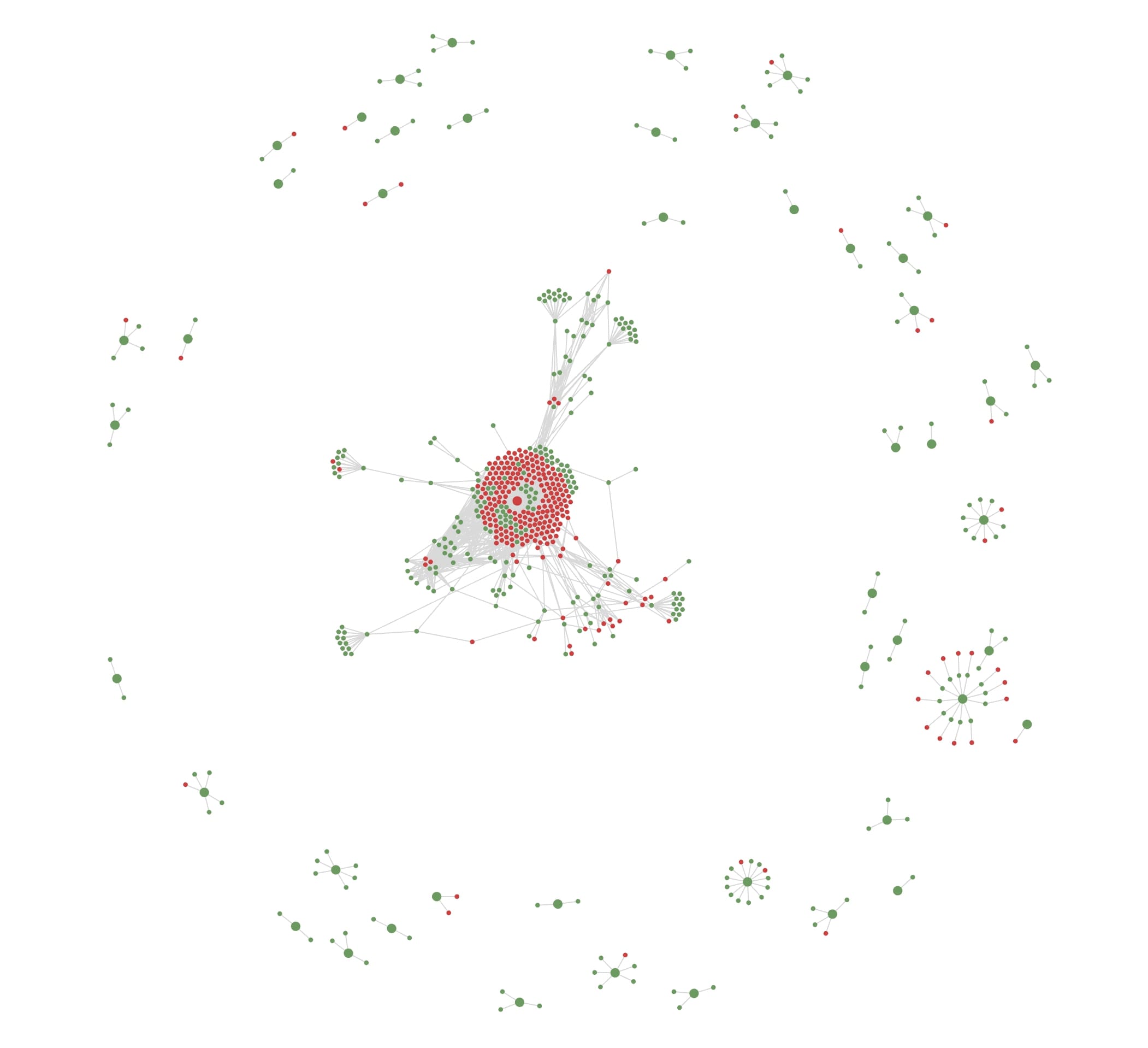
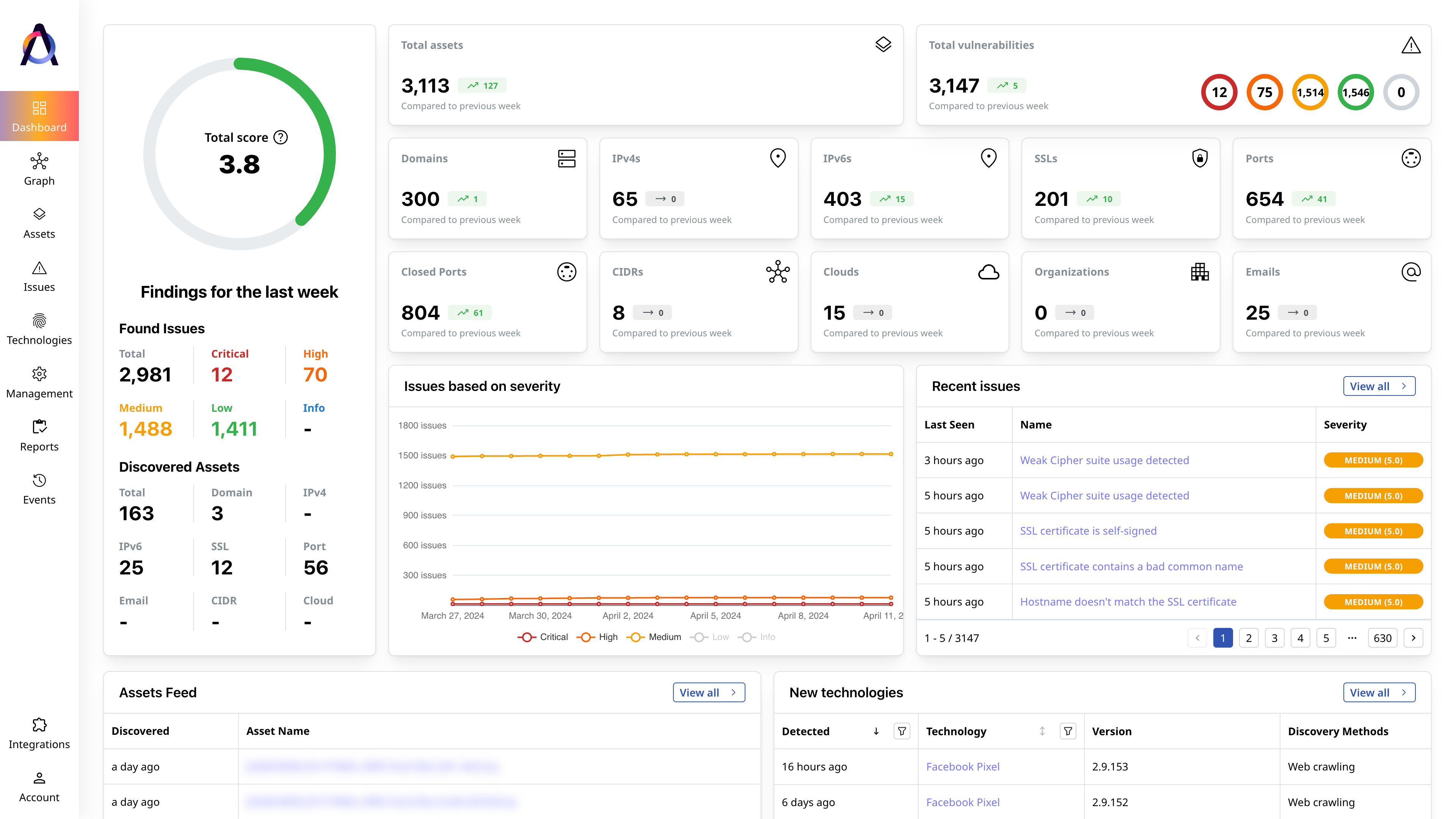
Find all assets tied to your public-facing IT environment
Obtain and maintain visibility over public-facing assets that threat actors may target.
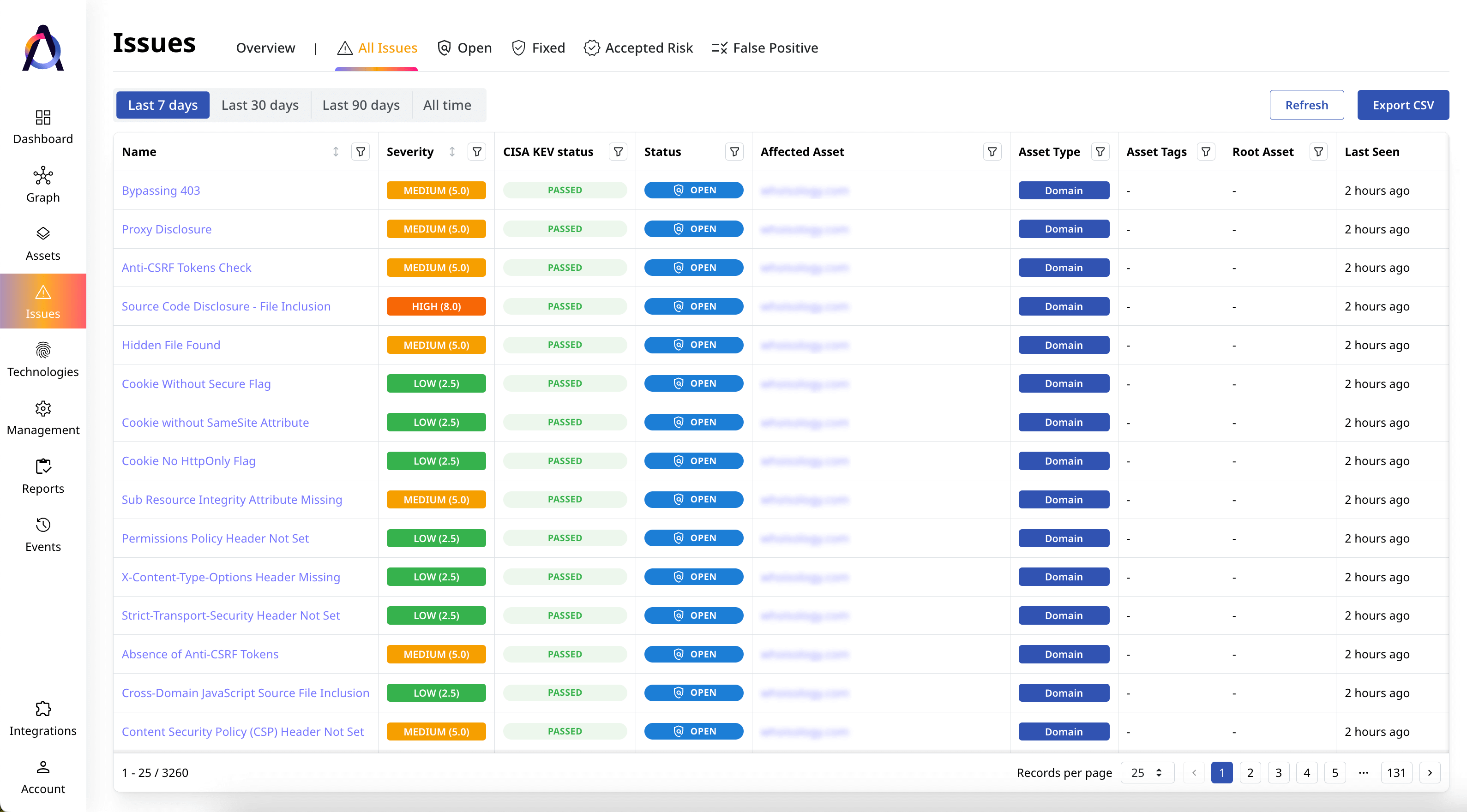
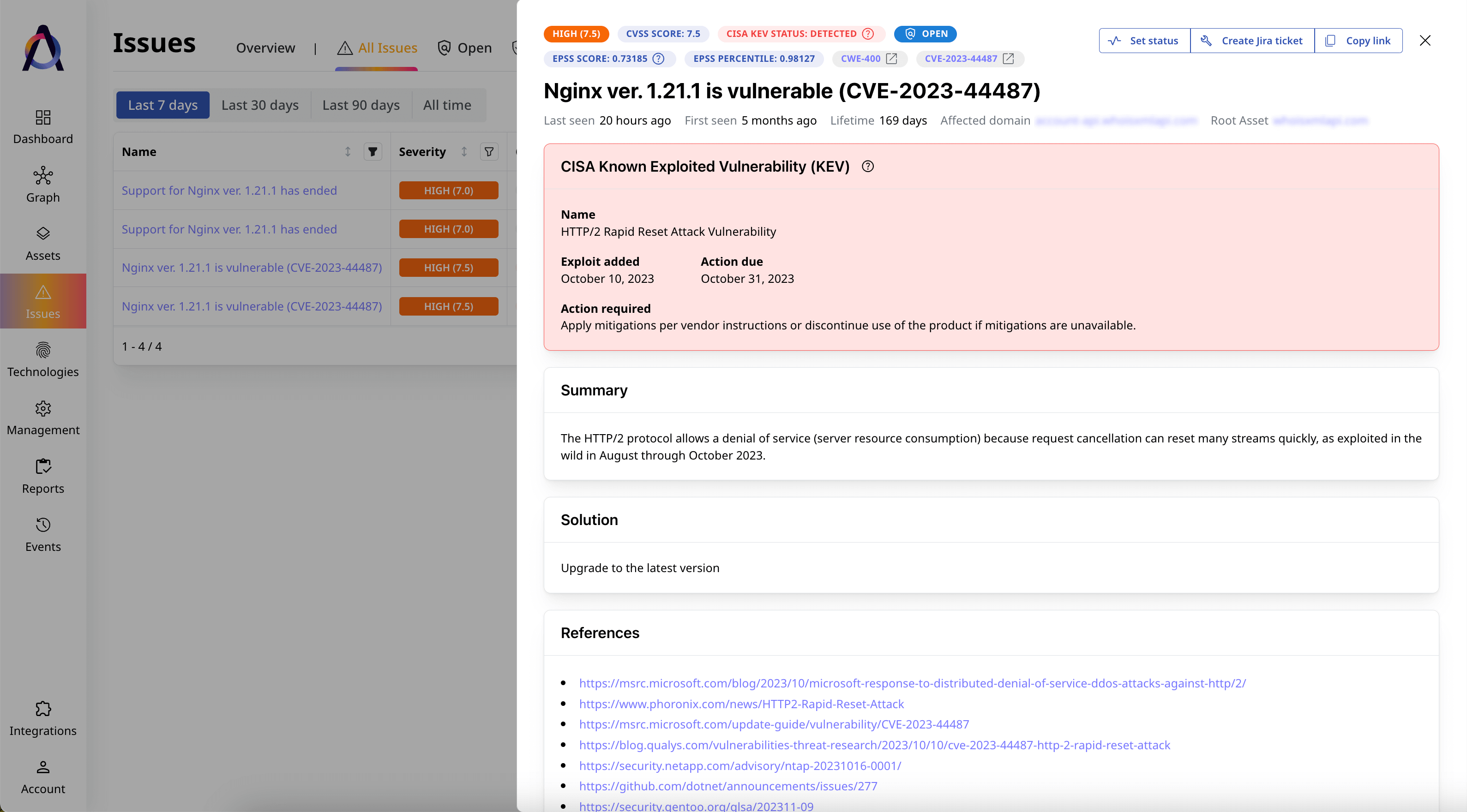
Identify and evaluate your risk exposure
Find and evaluate security gaps in your entire digital perimeter based on their severity and potential impact.
Safeguard platforms, user accounts, and intellectual property
Continuously scan your whole public-facing IT environment for new assets and security issues.
-
Superior Coverage
Discover twice as many external assets across varied asset types.
-
Third-Party Integration
Integrate project management and ticketing tools to streamline remediation.
-
Deeper Context
Drill down on each asset’s health, security risks, and connections.
What security experts say
Featured Resources

How Are Attack Vectors and Attack Surfaces Related?
Attack vectors and attack surfaces are deeply intertwined cybersecurity concepts. In a nutshell, an attack surface is the sum of all attack vectors in[...]

CWE Vs. CVE Vs. CVSS: What Are the Differences?
When protecting your digital infrastructure from threats, it’s critical to become familiar with security standards like CWE, CVE, and CVSS. These term[...]

How to Find Vulnerabilities in a Website
Website vulnerabilities are exploitable weaknesses that allow attackers to access data without authorization, steal sensitive information, or disrupt[...]