Blog
Trending Post

Your Guide to Port Scanning Attacks: Detection, Types, and Prevention
As gateways for data from the outside world, ports are destined to become prime targets for anyone intent on attacking a server. Port scanning attacks[...]
-
 Learn more
Learn moreCyberGlobal Australia Partners with Attaxion to Deliver Continuous Attack Surface Visibility to Australian Businesses
PRESS RELEASE DOVER, DE, UNITED STATES, May 26, 2026 — Attaxion has announced a strategic partnership with CyberGlobal A[...]
-
 Learn more
Learn moreNetFlow in Cybersecurity: The Ultimate Beginner’s Guide
Analyzing full packet captures (PCAPs) in Wireshark is almost a rite of passage in cybersecurity — no matter whether you[...]
-
 Learn more
Learn moreNetFlow Threat Hunting: How Network Flow Data Helps You Find Hidden Threats
NetFlow is not frequently discussed as a source of threat hunting data, but it deserves a seat at the table just as much[...]
-
 Learn more
Learn moreYour Guide to Port Scanning Attacks: Detection, Types, and Prevention
As gateways for data from the outside world, ports are destined to become prime targets for anyone intent on attacking a[...]
-
 Learn more
Learn more8 Free and Open-Source Vulnerability Management Tools
Open source has a massive footprint in the cybersecurity industry. For almost every security challenge, there is an open[...]
-
 Learn more
Learn more19 Vulnerability Management Metrics to Track (Internally and For Reporting)
You looked at the results from your most recent vulnerability scan, and there’s… a lot to take in. How do you tran[...]
-
 Learn more
Learn moreM&A Cybersecurity: Managing Cyber Risk for Buyers and Sellers
In high-stakes transactions such as mergers and acquisitions (M&A), speed often takes priority over security. But ov[...]
-
 Learn more
Learn moreNordic Revenue Partners with Attaxion to Deliver Accurate Asset Inventory Across the Nordic Countries
PRESS RELEASE DOVER, DE, UNITED STATES, February 16, 2026 — Attaxion has announced a partnership with Nordic Revenue, a[...]
-
 Learn more
Learn more10 Best Asset Discovery Tools
This post has been updated in February 2026 to cover cloud infrastructure discovery capabilities of the tools. Security[...]
-
 Learn more
Learn moreHow Digital Brand Protection Helps Against Impersonation
Brand reputation takes years to build, but a threat actor can tarnish it much faster by impersonating you online. [...]
-
![Vulnerability Assessment: Methodology and Types [and a Checklist]](https://attaxion.com/wp-content/uploads/2024/01/vulnerability-assessment.jpg) Learn more
Learn moreVulnerability Assessment: Methodology and Types [and a Checklist]
The sheer volume of potential attack vectors is staggering. In 2025 alone, 48,177 Common Vulnerabilities and Exposures ([...]
-
 Learn more
Learn moreAttaxion Now Has Domain Brand Monitoring Capabilities
DOVER, DE, UNITED STATES, January 22, 2026 — Attaxion is proud to introduce the new domain brand monitoring capabilities[...]
-
 Learn more
Learn moreCloud Security Assessment in 10 Steps
The cloud’s biggest advantage — quick scaling — is also the source of its main peril: clouds are hard to control. New as[...]
-
 Learn more
Learn moreIoC Threat Hunting: The 2026 Guide
As a threat hunter, you’ve probably been told countless times to hunt for things at the top of the Pyramid of Pain becau[...]
-
 Learn more
Learn moreHow To Maximize Attack Surface Visibility
One of the major obstacles standing in the way of an effective cybersecurity strategy is getting full attack surface vis[...]
-
 Learn more
Learn moreITCqure Partners with Attaxion to Strengthen Global Cyber Defense through Heightened Asset Visibility
PRESS RELEASE DOVER, DE, UNITED STATES, December 11, 2025 — Attaxion announces a strategic partnership with ITCqure, a g[...]
-
 Learn more
Learn more12 Best Network Security Monitoring Tools of 2025
If you ask five cybersecurity professionals: “What are network security monitoring tools?”, you might get five different[...]
-
 Learn more
Learn moreCyber Defense Partners with Attaxion to Deliver Proactive Protection and Faster Incident Response
PRESS RELEASE DOVER, DE, UNITED STATES, November 20, 2025 — Attaxion announces a strategic partnership with CyberDefense[...]
-
 Learn more
Learn moreAttaxion Launches REST API for Security Automation and Integration
DOVER, DE, UNITED STATES, October 17, 2025 — Attaxion is proud to announce the general availability of the Attaxion REST[...]
-
 Learn more
Learn moreAttaxion Releases Agentless Traffic Monitoring for Immediate Risk Prioritization
PRESS RELEASE DOVER, DE, UNITED STATES, August 25, 2025 — Attaxion announces the addition of the Agentless Traffic Monit[...]
-
 Learn more
Learn moreHow to Detect Exposed IP Addresses in Your Infrastructure
“What Internet-facing IP addresses do I have in my infrastructure?” This is a common question that security professional[...]
-
 Learn more
Learn moreUnderstanding Penetration Testing Scope
Your organization will likely need penetration testing at some point, whether for regulatory compliance or as part of a[...]
-
 Learn more
Learn moreSSRF vs. CSRF Vulnerabilities: Comparing Targets, Impact, and Mitigation Techniques
Server-side request forgery (SSRF) and cross-site request forgery (CSRF) are two types of attacks that allow attackers t[...]
-
 Learn more
Learn moreCVSS vs. EPSS: Which Vulnerability Scoring Do You Need?
The overwhelming number of vulnerabilities organizations face—and attackers can exploit—makes it impractical and even im[...]
-
 Learn more
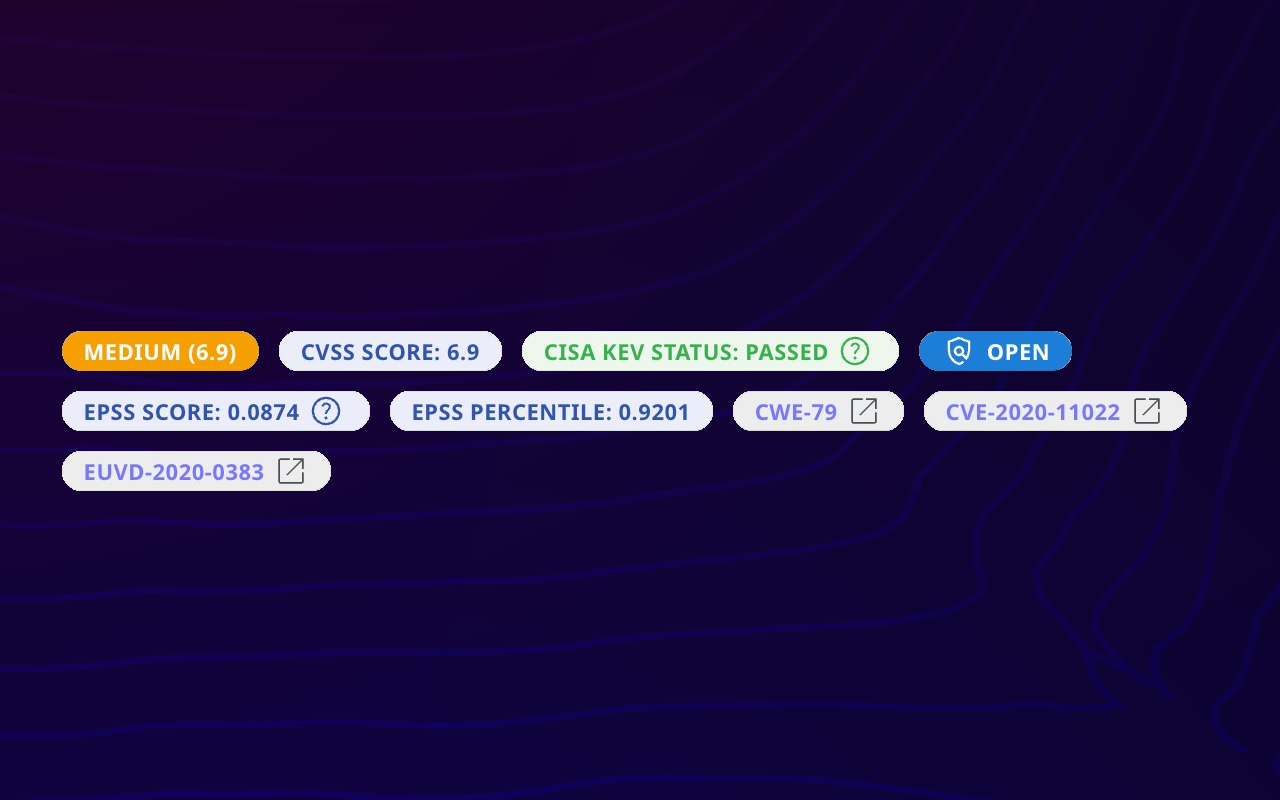
Learn moreAttaxion Becomes the First EASM Platform to Integrate ENISA’s EU Vulnerability Database (EUVD)
PRESS RELEASE DOVER, DE, UNITED STATES, May 21, 2025 — Attaxion, the external attack surface management (EASM) vendor wi[...]
-
 Learn more
Learn moreAttack Surface Management vs. Vulnerability Management: What’s the Difference?
New cybersecurity abbreviations appear faster than professionals manage to memorize them. So, when people see yet anothe[...]
-
 Learn more
Learn moreCWE Vs. CVE Vs. CVSS: What Are the Differences?
When protecting your digital infrastructure from threats, it’s critical to become familiar with security standards like[...]
-
 Learn more
Learn moreSubdomain Security: How Forgotten Assets Can Become Vulnerable Gateways for Attackers
“Out of sight, out of mind” is true even in cybersecurity. Assets that are not visible to the security team are often fo[...]
-
 Learn more
Learn moreNew EU Product Liability Directive: What Software Companies Need to Know
Software supply chain vulnerabilities are a multimillion-dollar problem, according to a study by Juniper Research, and i[...]
-
 Learn more
Learn moreSAST Vs. DAST Vs. EASM: Selecting the Right Tools for You
Modern cybersecurity is littered with too many acronyms that sometimes leave even seasoned professionals scratching thei[...]
-
 Learn more
Learn moreStaying Ahead of Domain Hijacking: The Critical Risks of Missed Domain Renewals
Two-thirds of security breaches can be attributed to human error, according to Verizon’s 2024 DBIR. Cyber attackers are[...]
-
 Learn more
Learn more10 Critical Attack Surface Metrics to Track
With recent regulatory changes pushing cybersecurity to the boardroom, effective attack surface monitoring and visualiza[...]
-
 Learn more
Learn moreTechnology Vulnerability Management Process with EASM
Technology Vulnerability Management Process with EASM Modern cybersecurity solutions allow you to partially automate vul[...]
-
 Learn more
Learn moreHow BOD 23-01 Can Enhance Federal Network Asset Visibility and Vulnerability Detection
It’s no secret that governments are prime cyber attack targets the world over. And why not? They hold very sensitive inf[...]
-
 Learn more
Learn moreThe New SEC Rules and What They Mean for CISOs
The onslaught of cyber attacks in the past years has prompted government agencies to take the lead in improving cybersec[...]
-
 Learn more
Learn moreWhat Does the Threat Landscape Look Like According to the 2024 Verizon DBIR?
When we know what threats we’re up against, we can prepare better. For this reason, reports like Verizon’s annual Data B[...]
-
 Learn more
Learn moreDetecting the Top 25 CWEs with EASM
Everything happens for a reason. For most vulnerabilities on the Common Vulnerabilities and Exposures (CVE) list, the re[...]
-
 Learn more
Learn moreThe Importance of Asset Attribution to External Attack Surface Management
The prevalence of cyber attacks has become a harsh reality. A study shows that 69% of organizations have fallen victim t[...]
-
 Learn more
Learn moreNIS 2 Compliance: From Asset Discovery to Risk Management
No entity across industries and regions is safe from cyber attacks. The European Union (EU) Agency for Cybersecurity (EN[...]
-
 Learn more
Learn moreUsing EASM Together With the Mitre ATT&CK Framework
External Attack Surface Management (EASM) platforms and attackers employ similar reconnaissance techniques for sca[...]
-
 Learn more
Learn moreSecuring ISO 27001 Compliance: Attack Surface and Risk Management Essentials
Building customer trust takes a lot of hard work, and a single security incident can jeopardize it all. In fact, IBM[...]
-
 Learn more
Learn moreOWASP Top 10 Vulnerabilities Detection through EASM
Threat actors strategically capitalize on their knowledge of existing vulnerabilities to target susceptible victims. The[...]
-
 Learn more
Learn moreOvercoming the Top SOC Challenges with EASM
A day in the life of a security operations center (SOC) analyst likely involves sifting through mountains of data and al[...]
-
 Learn more
Learn moreYour Digital Supply Chain Is Expanding Your Attack Surface
As organizations increasingly rely on third-party vendors and suppliers for their day-to-day operations, their digital e[...]
-
 Learn more
Learn moreScaling Up? 4 Critical Questions to Manage Your Expanding Attack Surface
Standing still is not an option for organizations that want to succeed. Companies must constantly strive for growth by e[...]
-
 Learn more
Learn moreActive and Passive Vulnerability Scanning: What Is the Difference?
Vulnerability scanning is an integral part of attack surface analysis, helping security teams identify security issues,[...]
-
 Learn more
Learn moreTypes of Web Application Attacks
Web applications are a prime cyber attack target because they often contain sensitive data, such as customer information[...]
-
 Learn more
Learn more4 Common Network Vulnerabilities
Although threat actors aim to take advantage of the latest vulnerabilities, there are also recurring weak aspects of net[...]
-
 Learn more
Learn morePenetration Testing versus Vulnerability Scanning: How Do They Differ?
Penetration testing or pentesting for short and vulnerability scanning are critical processes that help organizations id[...]
-
 Learn more
Learn moreHow to Find Vulnerabilities in a Website
Website vulnerabilities are exploitable weaknesses that allow attackers to access data without authorization, steal sens[...]
-
 Learn more
Learn moreHow Are Attack Vectors and Attack Surfaces Related?
Attack vectors and attack surfaces are deeply intertwined cybersecurity concepts. In a nutshell, an attack surface is th[...]