Best Intruder.io Alternative [2026]
This article has been last updated in January 2026 to cover the latest Intruder pricing changes and the most recent versions of both Intruder and Attaxion
Intruder.io is a cloud-based vulnerability scanner with attack surface management capabilities that’s been around for almost a decade. Intruder helps organizations protect their attack surface and comply with regulations such as PCI or GDPR.
Attaxion is a modern alternative to Intruder.io that also supports vulnerability management and external attack surface management with a heavy emphasis on attack surface discovery — something that Intruder only offers on enterprise plans. Both Attaxion and Intruder have their own strengths and weaknesses. Let’s take a look at how these two platforms compare and see if Attaxion can be considered a solid Intruder alternative.
Since both solutions can be your go-to tools for vulnerability management, we’ll assess them from this perspective, going through 5 stages of the vulnerability management process:
- asset discovery and inventory
- vulnerability scanning
- vulnerability prioritization and risk analysis
- vulnerability prioritization and mitigation
- continuous monitoring.
But we’ll start with pricing.
 PART 1
PART 1
Pricing
Free trial
Both Attaxion and Intruder offer a free trial, so that you can get a taste of the platform’s capabilities. Attaxion offers a 30-day trial with all features included. Intruder’s trial is 14-days long and is limited to one of its lower tiers called Cloud with licenses for up to 5 infrastructure targets or web applications. Also, Intruder requires a credit card to start the free trial, otherwise you’re stuck with a training dummy infrastructure.
In both cases, free trials are available to everyone on demand – you don’t need to contact sales to start using Attaxion or Intruder.io. We will be mostly evaluating Intruder’s Cloud plan in this comparison.

Intruder.io pricing and plans
When it comes to paid plans, Intruder’s pricing depends on two main factors: which of the four tiers you choose and how many web apps or targets you want to cover. Intruder also regularly increases its pricing, so its better to check it on their pricing page, even though it lost some of its transparency lately.
The most basic tier in Intruder is called Essential – it’s very limited, as it doesn’t have any integrations and only allows you to run one scheduled scan. This tier is not very well suited for doing vulnerability management properly, as it’s limited to one scheduled scan per month. Basically, it’s an on-demand scanner. So, we won’t be considering it for the purposes of this article.
The next is the Cloud tier that Intruder added in April 2025. It offers everything in Essential plus weekly network scans, integrations, and automated scans. Also, Cloud plan relies on a different set of vulnerability scanners, but we’ll discuss that in more detail later.
Cloud is followed by the Pro tier, which offers almost all the features Intruder has in its sleeve. It has everything in Cloud plus internal scanning, and, again, a different vulnerability scanner.
Finally, there’s Enterprise tier, previously called Premium, and before that, Custom. It has everything in Pro plus asset discovery (that is lacking on all other plans), daily network scans, so-called rapid response scans, and more. There’s no way to pay for Enterprise with a credit card, you’ll need to contact sales and discuss the pricing with them. Intruder’s pricing also occasionally mentions Vanguard plan in the FAQ, but we couldn’t find any information about it — it seems to be a legacy option.
Unlike Enterprise, Intruder’s Essential, Cloud, and Pro plans are self-serve. Previously, Intruder had transparent pricing and a calculator which you could use to calculate how much protection for your infrastructure with a specific number of infrastructure targets and web apps would cost you. However, recently they’ve removed the calculator and all mentions of prices. So, 2025 Intruder pricing information is limited to this:
- Essential plan starts at $130/month
- Cloud plan starts at $260/month (a yearly plan can be bought on Amazon for $2,870 [as of January 2025])
- Pro plan starts from $434/month (paid yearly)
The prices are for 5 infrastructure licenses and do not include VAT. If you’re based in Europe, you’ll see the same numbers, but in Euro.
An infrastructure license covers infrastructure targets (websites/hostnames/IPs/endpoints). On top of that, Intruder has application licenses that you’ll need to purchase if you want to use authenticated web application scanning, and API licenses for API schema. Asset discovery is a part of the Enterprise plan which is calculated based on your specific requirements and the size and complexity of your systems.
Attaxion Pricing
Attaxion offers all it has right away – and the functionalities are available on every tier, including asset discovery that Intruder only has on the Enterprise plan. That includes an advanced web application scanner, automated scans, integrations, and more. The only significant difference between plans is in the number of assets covered.
Attaxion is priced by asset. The pricing starts at $129/month for up to 40 assets (if billed monthly), which include domains, subdomains, IPs, cloud infrastructure instances, CIDRs, and more. Here are some details on assets and asset types in Attaxion. The next plan is called Plus, and it offers 120 assets. Finally, there’s the Business plan with 360 assets. Everything above that should be discussed with sales individually, but the price per asset only gets cheaper on larger plans.
If paid yearly, Attaxion also gets cheaper – down to $1,290 a year for the Starter plan.
How They Compare
Due to significant differences in pricing models, it’s hard to compare prices. Previously, both tools were on the less expensive side of the spectrum. However, in 2024 and in 2025, Intruder has increased the prices, and G2 users note that they are “more expensive than competitors” or “not startup-friendly” anymore.
| Intruder.io vs Attaxion: Pricing | ||
| Attaxion | Intruder | |
| Pricing monthly | Starts at USD $129/month for up to 40 assets | Starts at USD $260/month for 5 infrastructure targets (Cloud plan) |
| Pricing yearly | Starts at $1,290/year for up to 40 assets | Starts at USD ~ $2,870/year for 5 infrastructure targets (Cloud plan on Amazon) |
| Assets covered at the starting price | 40 (all types) | 5 |
| Free trial | ✅ (30 days) | ✅ (14 days) |
 PART 2
PART 2
Asset Discovery and Inventory
Asset discovery and inventory is the first step of the vulnerability management process. And this is, perhaps, where Intruder.io and Attaxion differ the most. For Attaxion, asset discovery is its core specialization, while Intruder doesn’t offer to discover assets on plans other than Enterprise, except via cloud connectors.
| Intruder.io vs Attaxion: Asset Discovery | ||
| Attaxion | Intruder | |
| Automatic asset discovery through cyber reconnaissance | ✅ | ❌ |
| Types of assets discovered | 10+: – Domains – Subdomains – IP addresses – Ports – Organizations – Open ports – Email addresses – Clouds – CIDRs – SSL Certificates | 2 (for manually added assets): – Ports – SSL Certificates |
| Cloud environments sync | – AWS – Google Cloud – Microsoft Azure – Digital Ocean | – AWS – Google Cloud – Microsoft Azure |
| Asset coverage | ✅ Highest | ❌ Not applicable |
| Dependency graph | ✅ | ❌ |
Intruder.io Doesn’t Offer Cyber-Reconnaissance on PLG Plans
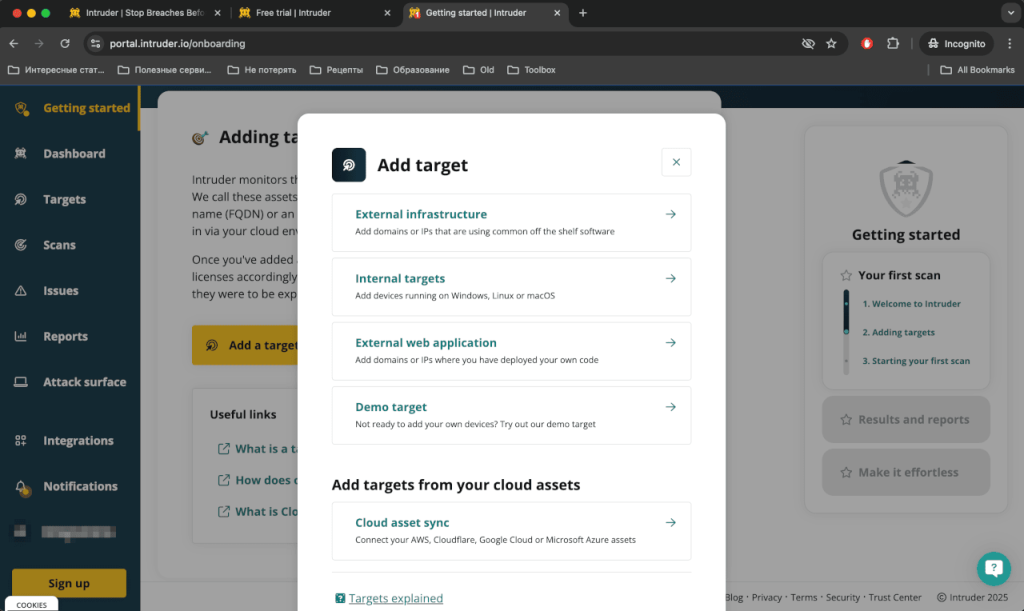
Using Intruder begins with adding targets. The platform completely relies on you knowing about all the assets that you want to scan, and meticulously adding them to Intruder’s interface as targets or web applications.
Once you’ve added an asset, Intruder.io will be able to scan it for vulnerabilities, as well as find open ports and related SSL certificates. But it doesn’t provide subdomain enumeration functionality, for example, except on Enterprise plans. Otherwise, you’ll need to add subdomains manually, one by one.
Another option is to add an integration with your cloud environment (available on plans starting with Cloud) – be it AWS, GCP, or Azure. In this case, you can choose if you want to automatically sync assets, and Intruder will add everything in your cloud account as infrastructure targets.
Attaxion Offers Broad Asset Coverage
Attaxion’s approach is very different from how Intruder.io works. You can add a number of root assets to Attaxion (domains, IP addresses, cloud accounts), and then it will discover related assets automatically.
Attaxion’s set of cyber reconnaissance techniques allows it to find associated subdomains, IP addresses, open and closed ports, SSL certificates, and so on. It can even find exposed email addresses associated with the root asset.
So, unlike Intruder on all self-serve plans, Attaxion can help you protect not only the assets you are aware of and added to the interface, but also assets you didn’t even know existed.
Attaxion’s asset discovery capabilities are among the best on the market – that’s one of its true strengths. In addition to finding new assets, Attaxion can show how they are connected, drawing a dependency graph that can give an idea about potential attack paths adversaries can use. Intruder doesn’t show connections between assets
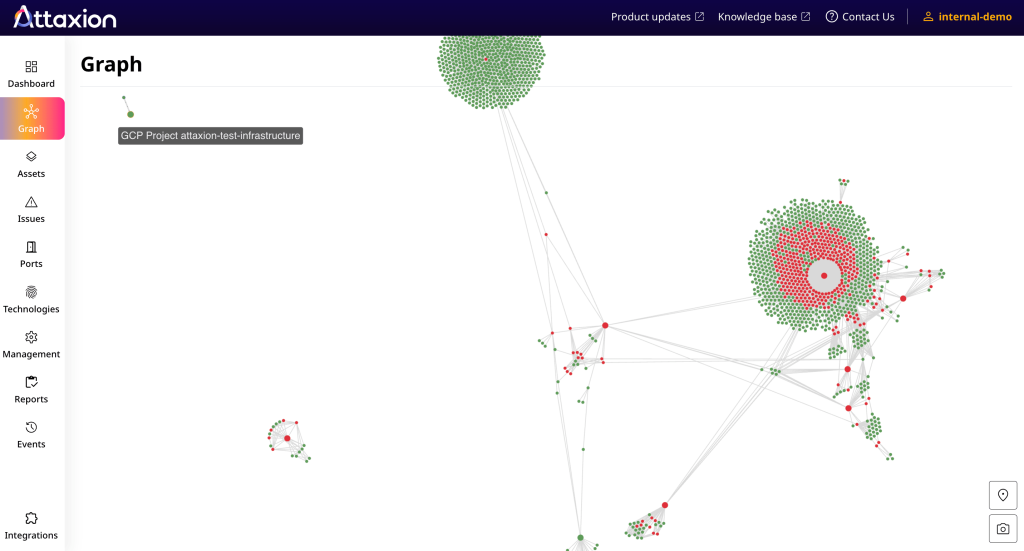
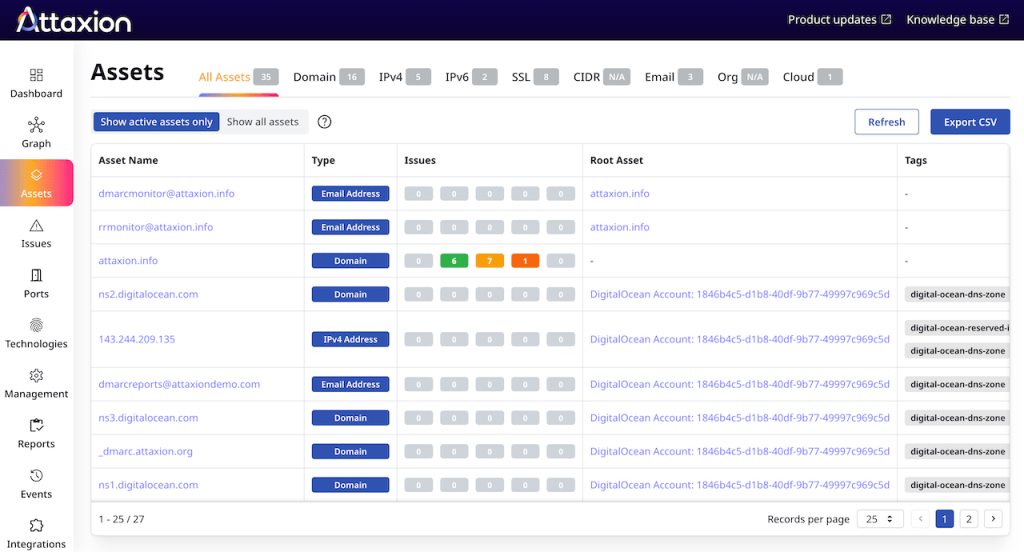
Unlike Intruder, Attaxion provides you with a complete asset inventory. For each asset, you can see its type, how many security issues of different severity it has, when it was last seen, and so on. Attaxion allows you to filter the list of assets by each of these parameters, as well as add tags.
With Attaxion, you can also switch between scan types: it offers stealthy passive scanning in addition to the more advanced active scanning. Active scanning allows you to find more assets, but, unlike passive scanning, it can be detected by intrusion detection systems (IDS).
How They Compare
To sum it up, when it comes to asset discovery, Intruder only offers cloud connectors on most plans, while Attaxion has a set of advanced cyber reconnaissance techniques for discovering known and unknown assets and mapping the entire external attack surface of the organization. Attaxion allows you to create and continuously update your external asset inventory.
 PART 3
PART 3
Vulnerability Detection
After the assets have been discovered, vulnerability management platforms rely on vulnerability scanners to find issues, and then filter out false positives.
| Intruder.io vs Attaxion: Vulnerability Detection | ||
| Attaxion | Intruder.io | |
| Scanner | – Attaxion (proprietary) – OWASP ZAP | – OpenVAS (Essential) – OpenVAS + Nuclei (Cloud) – Tenable (Pro) – Tenable + Nuclei (Custom) – OWASP ZAP (for web applications only) |
| Scanning | Continuous | – Scheduled – Triggered – Emerging Threat scans (Cloud and above) – Rapid Response scans (Enterprise) |
| Easy user interface | ✅ | ✅ |
| Technology fingerprinting | ✅ | ❌ |
Intruder’s Vulnerability Detection Capabilities
Depending on the plan that you choose, Intruder offers different vulnerability scanners:
- On Essential, you get OpenVAS – an open-source full-fledged vulnerability scanner, developed by Greenbone.
- On Cloud, Intruder combines OpenVAS with Nuclei – another open-source scanner.
- On Pro, instead of both open-source tools, Intruder.io offers to scan your infrastructure with Tenable Nessus, theoretically a more advanced vulnerability scanner.
- On Custom plans, Intruder combines Tenable Nessus with Nuclei.
- For web applications, Intruder relies on OWASP ZAP by Checkmarx.
Intruder.io offers to run network scans on a regular basis – weekly, monthly, or quarterly (with daily scans available on custom plan). You can also initiate a vulnerability scan manually or set up scheduled scans.
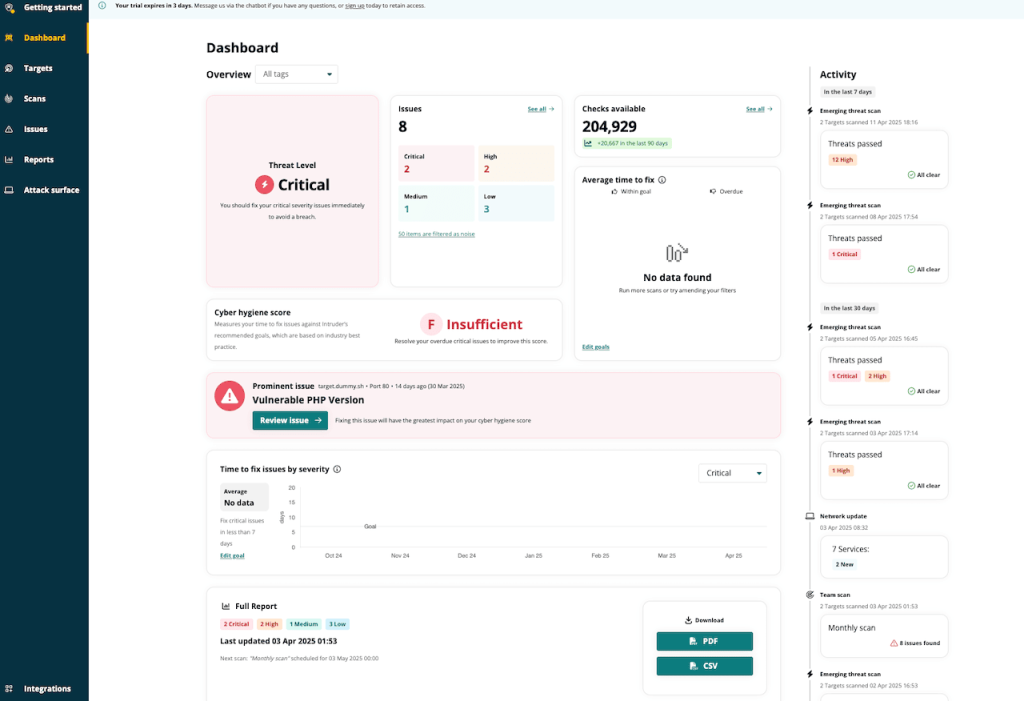
In addition to that, on Cloud plan and above Intruder.io offers to run so-called Emerging Threat scans – automatically initiating scans when new vulnerabilities are added to its database.
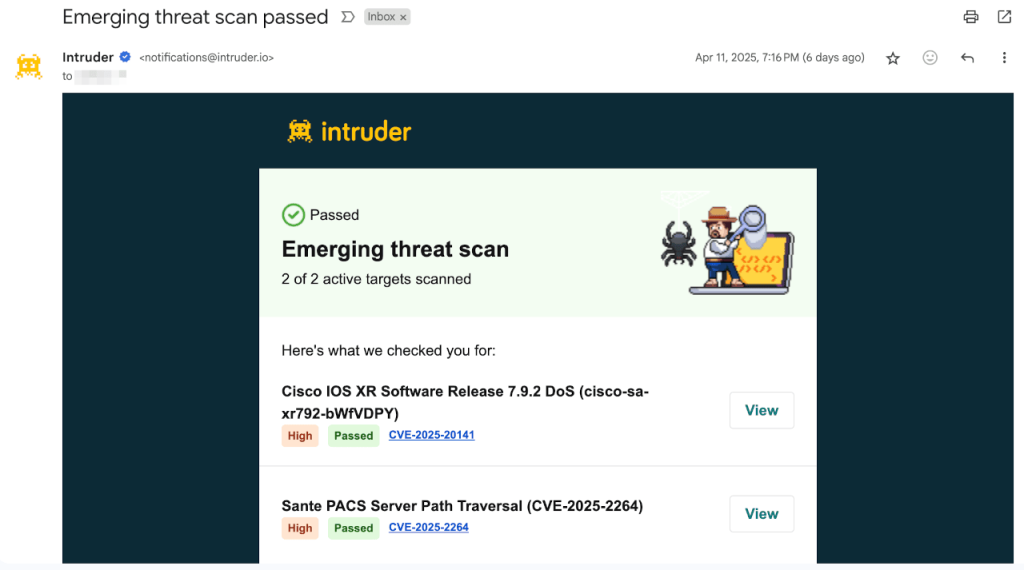
On Enterprise plan, it adds so-called Rapid Response scans – scanning for threats that are actively exploited in the wild at the moment.
Intruder offers authenticated scanning for web applications and API schema for testing APIs.
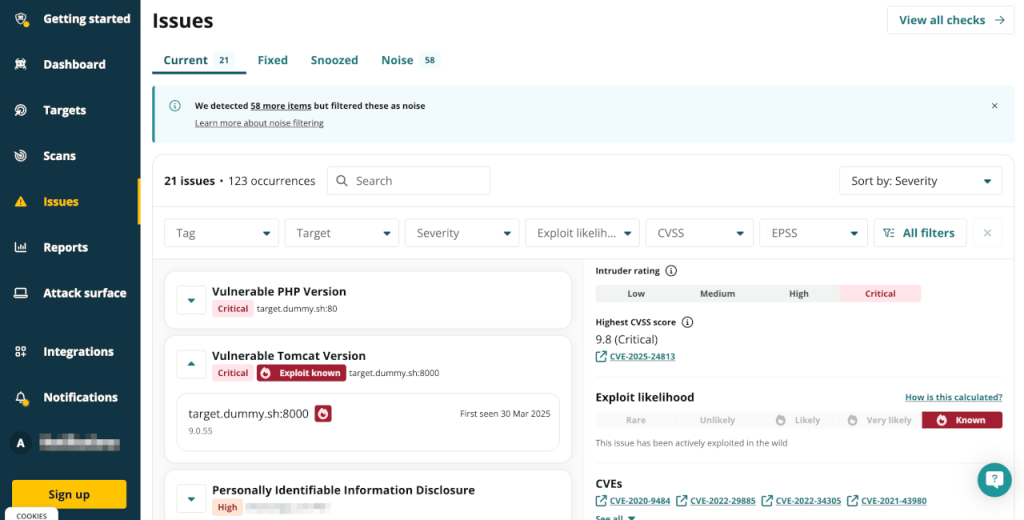
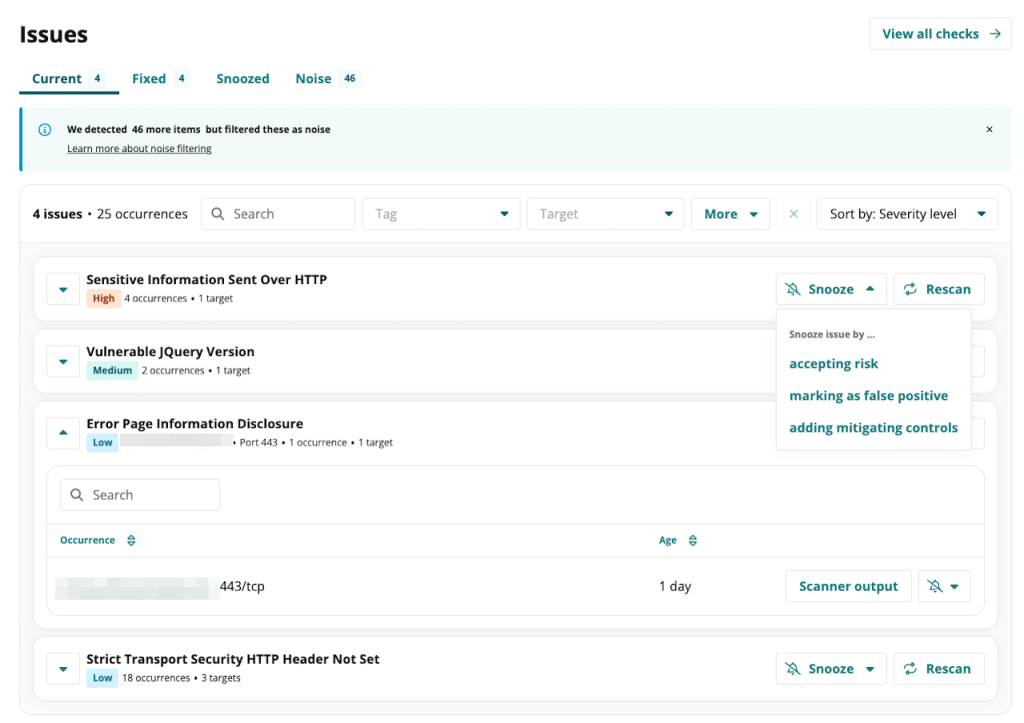
Some issues that Intruder finds, it filters out as noise. According to the documentation, these are the issues that they “deem informational rather than actionable.” You can still get access to the list of “noisy” issues as well, if you want to.
Attaxion’s Vulnerability Detection Capabilities
Attaxion uses its own proprietary scanner to scan for vulnerabilities in the assets that it discovers (and those that you add manually as root assets as well).
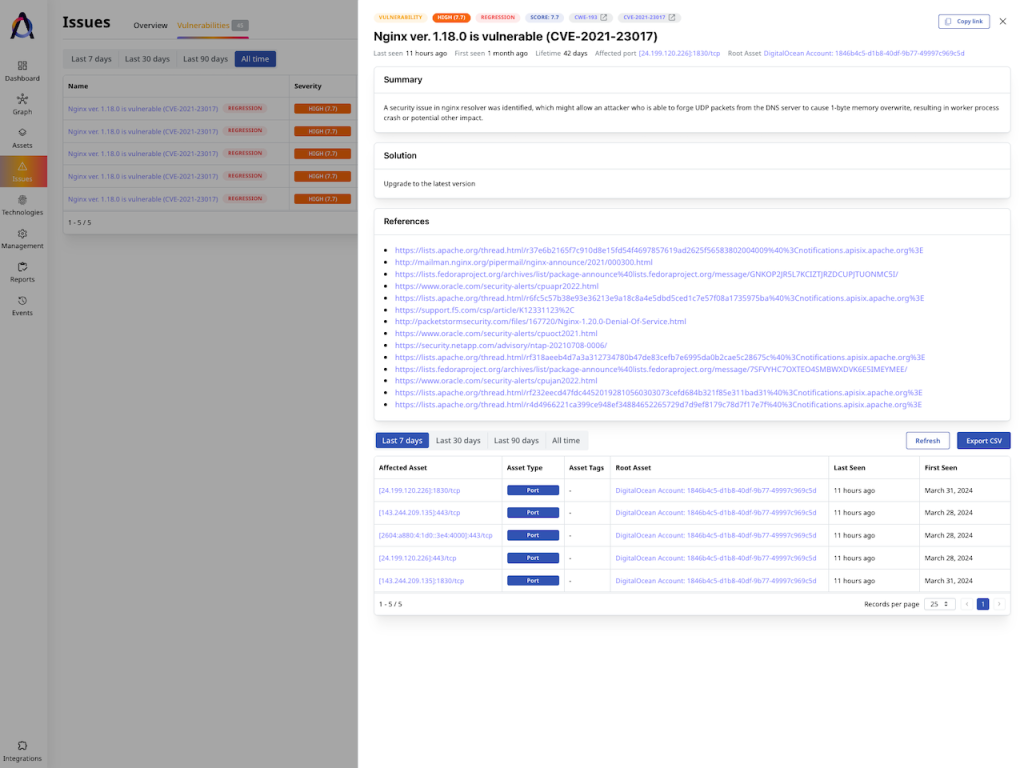
The databases Attaxion uses are up to date with Mitre’s CVE and CWE databases.
Attaxion’s approach to scanning is also different from Intruder’s. Instead of offering daily or manual scans, Attaxion relies on continuous scanning. It constantly keeps going through the organization’s assets, trying to discover new ones and scanning the already discovered ones for vulnerabilities.
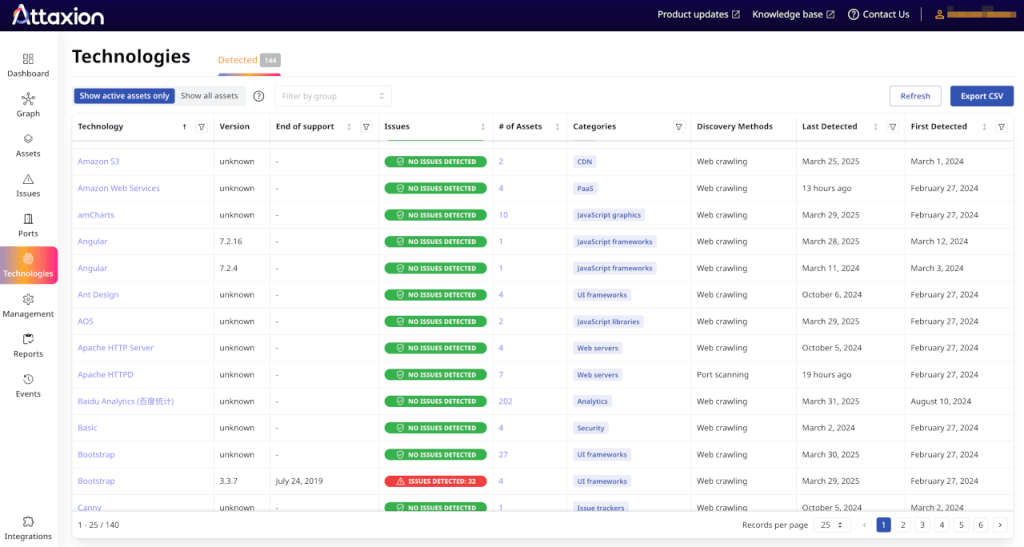
In addition to a list of vulnerabilities, Attaxion also builds a list of technologies such as SaaS platforms or frameworks associated with the asset. In the list, Attaxion highlights vulnerable technologies.
Technology fingerprinting allows you to quickly sort assets by technology, helping with prioritization and remediation. Intruder detects a much narrower list of technologies and doesn’t offer a centralized database for it.
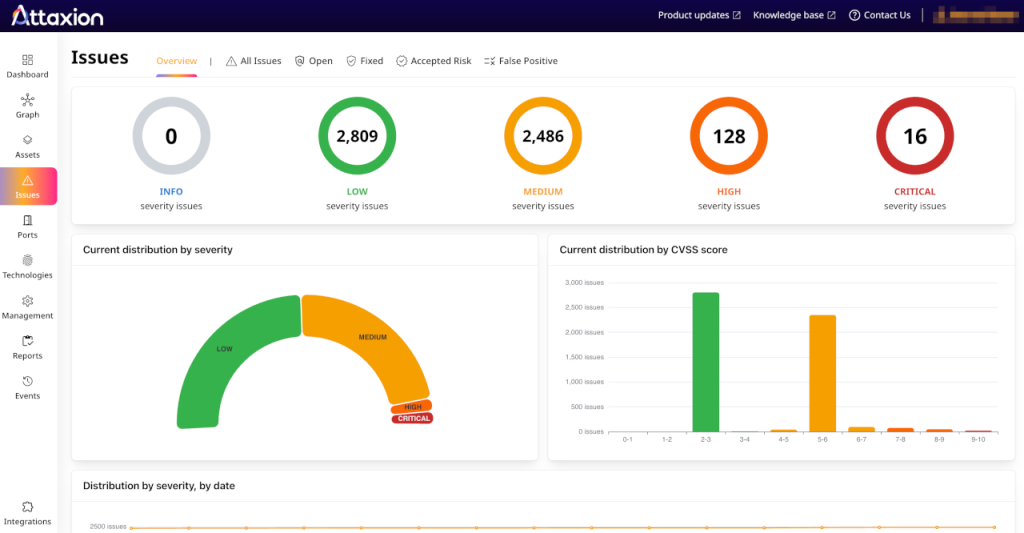
Other than that, Attaxion’s capabilities in vulnerability scanning are similar to those of Intruder: it provides a dashboard with distribution of issues by severity, and a list of issues with descriptions, dates, related assets, and remediation suggestions.
Both Intruder and Attaxion link to sources with more information about vulnerabilities.
How They Compare
When it comes to vulnerability detection, Intruder’s strong side is the ability to run Emerging Threat and Rapid Response scans. It also offers a broad variety of scanners and their combinations on different plans.
Attaxion’s strong sides are continuous scanning and technology fingerprinting. When it comes to the performance of the scanners, in our test, Attaxion was able to find more vulnerabilities than the Cloud version of Intruder.
 PART 4
PART 4
3. Vulnerability Prioritization
After finding all vulnerabilities, the next task is to prioritize them. Here, the two platforms have similar functionality.
| Intruder.io vs Attaxion: Vulnerability Prioritization | ||
| Attaxion | Intruder.io | |
| Dashboard | ✅ | ✅ |
| Vulnerability scoring parameters | CVSS, EPSS, CISA KEV, severity | CVSS, EPSS, CISA KEV, severity |
| Proprietary vulnerability score | ❌ | ✅ |
| Mark as false positive or accepted risk | ✅ | ✅ |
| Manual rescan trigger | ❌ | ✅ |
Vulnerability Prioritization with Intruder.io
Intruder offers a neat dashboard, where for each issue it provides data such as the description of the issue, which assets does it plague and how long ago has it been found. It also provides remediation suggestions.
For each issue, Intruder offers a list of related CVEs, exploitability data (EPSS) and exploitation likelihood (CISA KEV data). Based on the CVSS score for the CVE and the aforementioned data Intruder calculates its own severity score. However, as they say themselves, it is often equal to the CVSS score and deviates only rarely.
You can snooze an issue by marking it as an accepted risk, a false positive, or as something for which you’ve added mitigation controls. Also, you can manually trigger a rescan upon fixing the issue to ensure that it’s fixed.
Vulnerability Prioritization with Attaxion
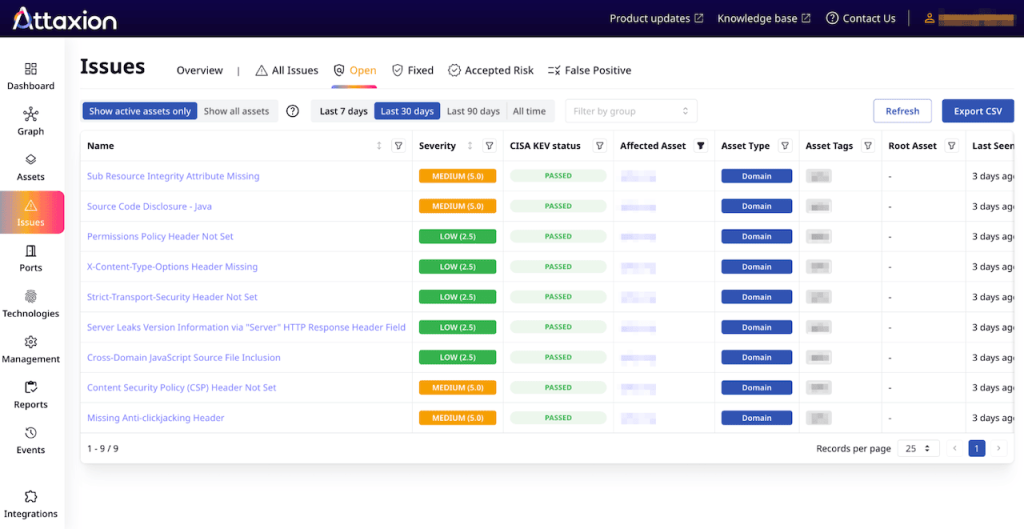
Attaxion is not very different from Intruder.io in this regard. It offers a list of all vulnerabilities that can be sorted by asset, by severity, CVSS score, CISA KEV data (whether it’s known or not known to be exploited in the wild) or date when the issue was last or first seen.
Above the list, there’s a dashboard that shows the distribution of vulnerabilities by CVSS and severity, as well as a graph showing how this has been changing over time. For each vulnerability with a CVE number Attaxion also provides its exploitability score – EPSS.
Attaxion similarly offers to mark issues as accepted risks, false positives, or fixed. There’s no option to manually trigger a scan though.
How They Compare
When it comes to prioritization, Intruder and Attaxion are almost equal. Both offer comprehensive vulnerability information with data on CVSS, EPSS, and CISA KEV data. Intruder goes one step further by offering its own custom vulnerability scoring system, but admits that in most cases it doesn’t differ from CVSS.
 PART 5
PART 5
Vulnerability Remediation
Vulnerability remediation in case of vulnerability management platforms usually boils down to providing suggestions and automating routine tasks such as creating tickets for support engineers. Attaxion and Intruder are quite similar in this regard, with Intruder offering some additional functions.
| Intruder.io vs Attaxion: Vulnerability Remediation | ||
| Attaxion | Intruder | |
| Remediation suggestions | ✅ | ✅ |
| Integrations with ticketing software | – Jira | – Jira – GitHub – GitLab – Azure DevOps – Service Now |
| Remediation dashboard | ❌ | ✅ |
| API | ✅ | ✅ |
Remediation with Intruder
For each vulnerability, in addition to description, Intruder offers remediation suggestions, as well as scanner output.
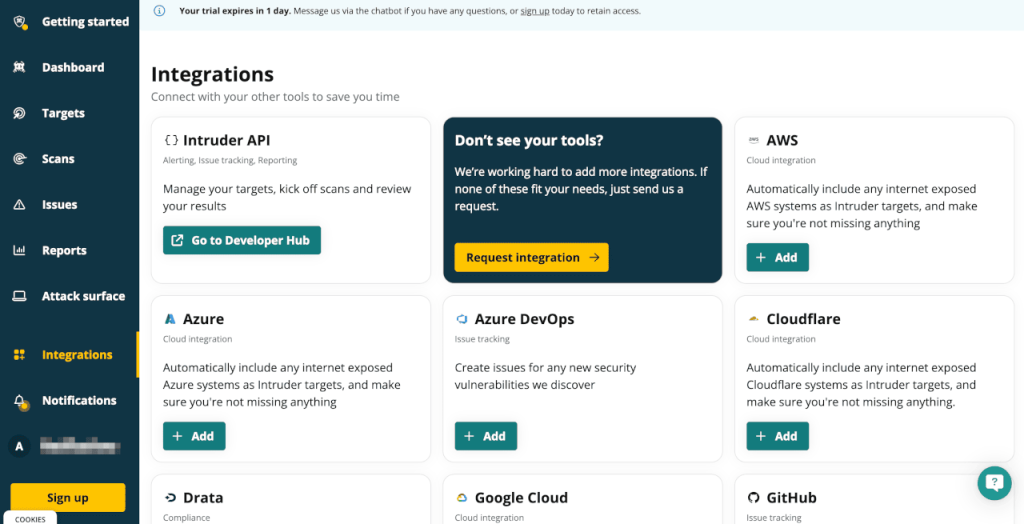
Intruder has a broad set of integrations that help simplify the remediation process. It can automatically create issues in Jira, GitHub, GitLab, Azure DevOps, and ServiceNow. It also offers an API to connect to other cybersecurity software. An integration with Zapier serves the same purpose.
Intruder offers very convenient dashboards that, among other things, show how the security team is handling vulnerability remediation. It provides metrics such as average time to fix issues (for different severities) and offers a graph to show how this changes over time.
Remediation with Attaxion
Attaxion also provides vulnerability description, evidence, and remediation suggestions from different sources, sometimes offering more detailed advice than Intruder.
When it comes to integrations relevant for the remediation stage, Attaxion has an integration with Jira that can create tickets pre-populated with vulnerability data. There aren’t any other integrations with ticketing software currently available, but you can reach out to Attaxion support and discuss the integrations you require with them. Alternatively, you can use Attaxion’s REST API to build your own.
How They Compare
Overall, when it comes to remediation, both platforms offer the two main things: advice and the ability to create tickets in bug trackers. Both Attaxion and Intruder refer to multiple sources for remediation suggestions. Both offer an API to deliver data to other tools.
However, Intruder has a broader set of integrations, as well as an option to track the team performance.
 PART 6
PART 6
Continuous Monitoring
We’ve described most of the features related to continuous monitoring in Asset Discovery and Inventory and Vulnerability Detection sections. Basically, both tools just keep using them continuously.
| Intruder.io vs Attaxion: Continuous Monitoring | ||
| Attaxion | Intruder | |
| Continuous attack surface discovery | ✅ | ❌ (only available on Enterprise plan) |
| Email notifications | ✅ | ✅ |
| Customizable notifications | ✅ (only by severity) | ✅ (by severity, scan type, scan results) |
| Integrations with messaging software | Slack | – Slack – Microsoft Teams |
Continuous Monitoring with Intruder.io
Intruder.io offers regular vulnerability scans and emerging threat scans (as well as rapid response scans on the Enterprise plan).
You can set up notifications for certain events that happen during scans.
Intruder offers very flexible email notifications, where you can choose to be notified about targets being affected or not affected by emerging threats, about completion of manual scans, and of the overall network status.
It also has integrations with Slack and Teams to send notifications via these messengers.
Continuous Monitoring with Attaxion
As mentioned earlier, Attaxion continuously keeps scanning the organization’s attack surface. Unlike Intruder’s self-serve plans, it can discover new assets that are not known to the organization – and run vulnerability scans against them.
Basically, Attaxion automates continuous vulnerability scanning of the whole dynamically changing external attack surface, while with Intruder, you’ll need to manually add new assets as they appear in the organization’s network, unless they are pulled from a cloud integration that you’ve added (or unless you pay premium for the Enterprise plan and where Intruder has asset discovery).
Attaxion also offers email notifications and has an integration with Slack.
How They Compare
Attaxion can continuously monitor the changing external attack surface, while Intruder.io keeps track only of the assets that you’ve added manually.
On the other hand, Intruder is more flexible when it comes to notifications, thanks to the broader set of integrations and extensively customizable email alerts.
 PART 7
PART 7
Conclusion
Intruder.io is a solid vulnerability management tool with a very user-friendly interface. Its strong sides are its dashboards, reports, and notifications, as well as a broad set of integrations. However, Intruder.io doesn’t offer asset discovery and subdomain enumeration (except for pulling assets from cloud connectors) on all plans but Enterprise.
Attaxion, on the other hand, has unique reconnaissance capabilities that allow it to discover and scan previously unknown external assets more effectively than the other tools on the market. It covers all 5 steps of the vulnerability management process, protecting the organization’s external attack surface on a completely different level and ensuring a strong security posture. However, as a platform that focuses on EASM, Attaxion doesn’t help with scanning internal assets.
Attaxion is also less expensive than Intruder, especially after Intruder’s pricing update in 2025, saving some of the precious cybersecurity budget for other necessary tools.
Ready to try Attaxion? Start a 30-day free trial, or request a personal demo.