NetFlow-Enhanced Exposure Visibility
NetFlow-Enhanced Exposure Visibility
Attaxion LiveSight
The only cybersecurity platform that shows not just what’s exposed across your attack surface, but who is actively communicating with your network in near real time.
 What You Can Do With Attaxion LiveSight
What You Can Do With Attaxion LiveSight
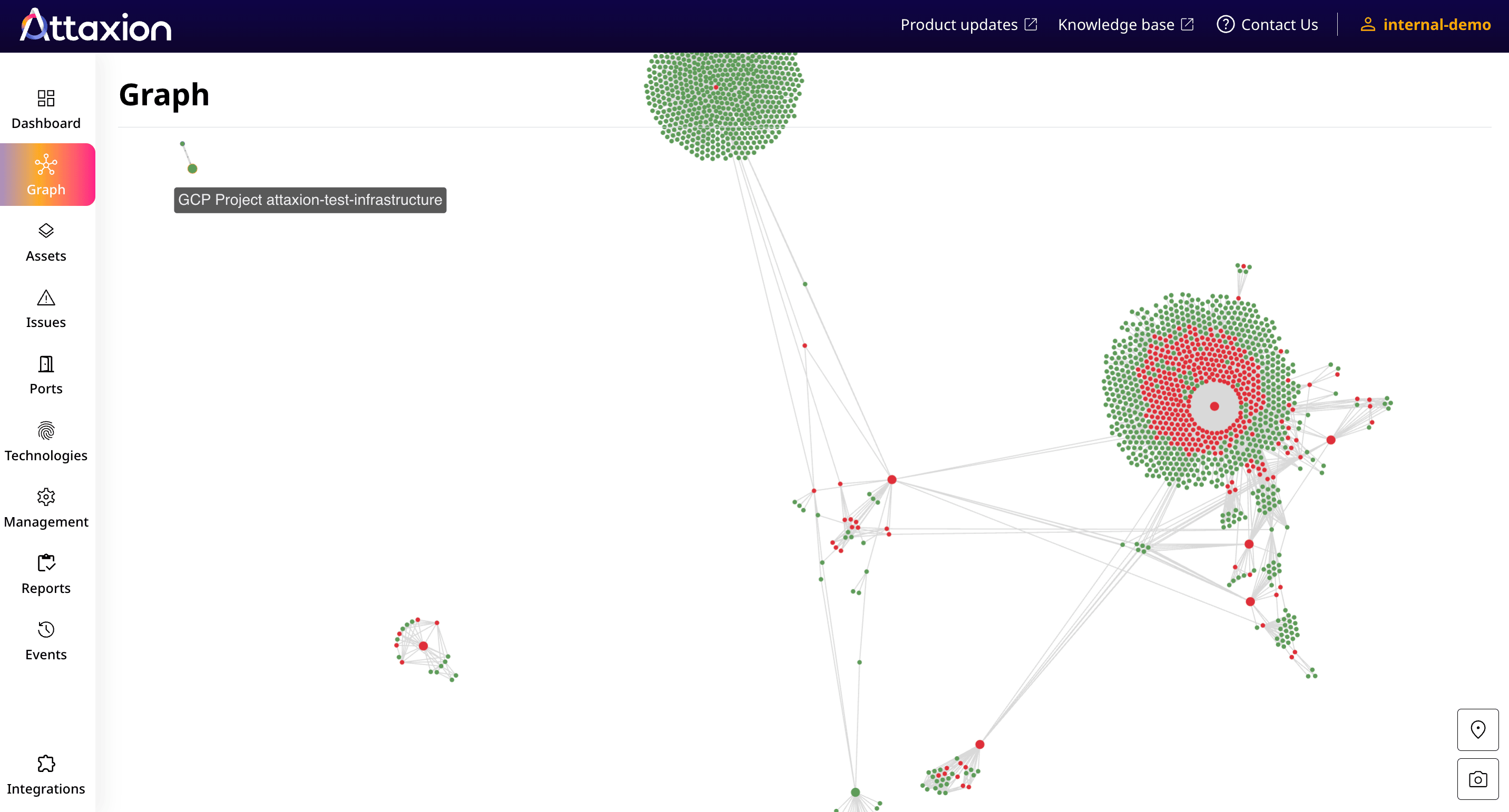
Find Assets and Issues Hidden from Traditional Discovery
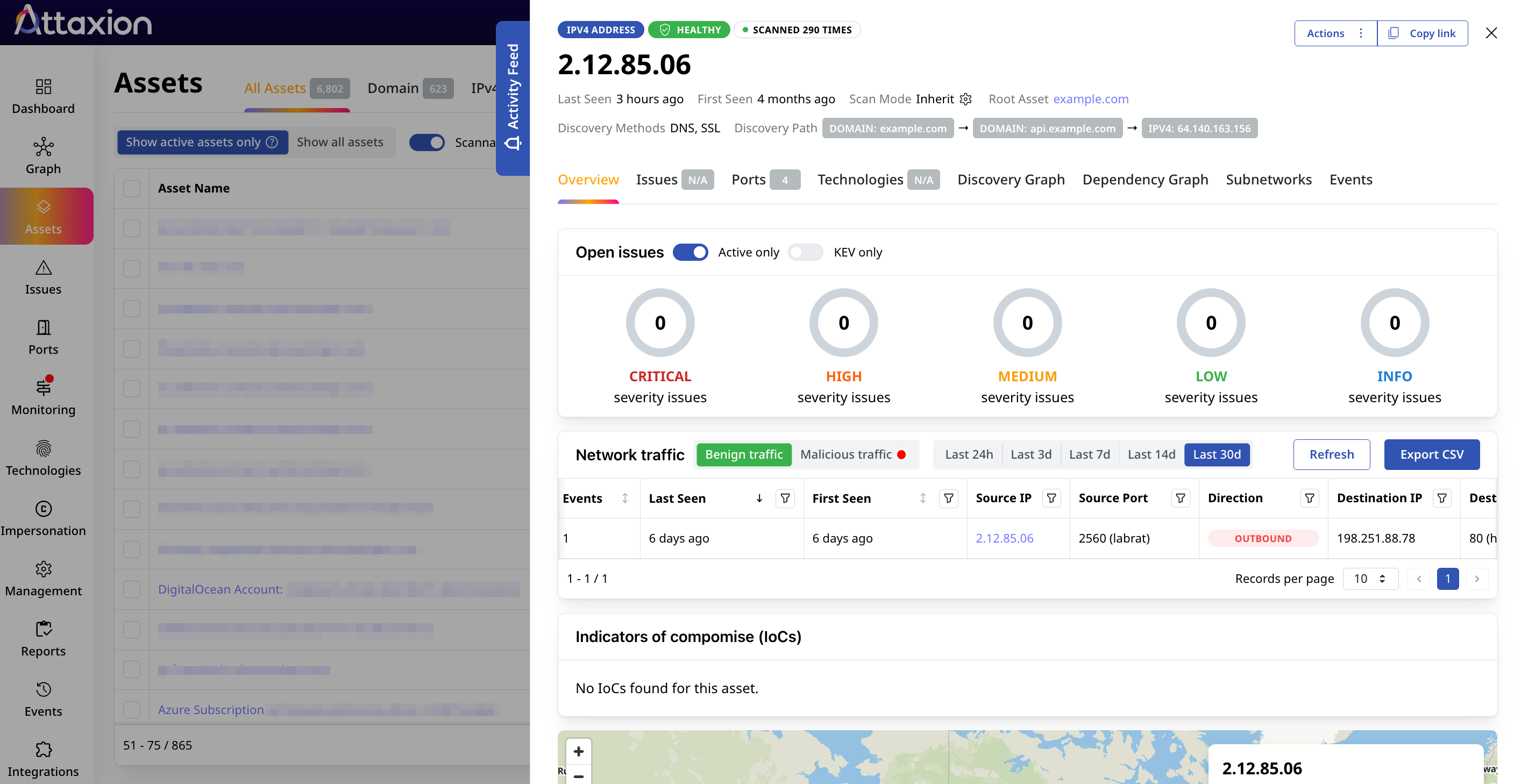
Attaxion LiveSight relies on NetFlow-enhanced discovery to bring to light your entire external attack surface, giving you extended, near real-time visibility into your assets, their vulnerabilities, and their network activity.
Prioritize Issues Based on Real, Measurable Activity
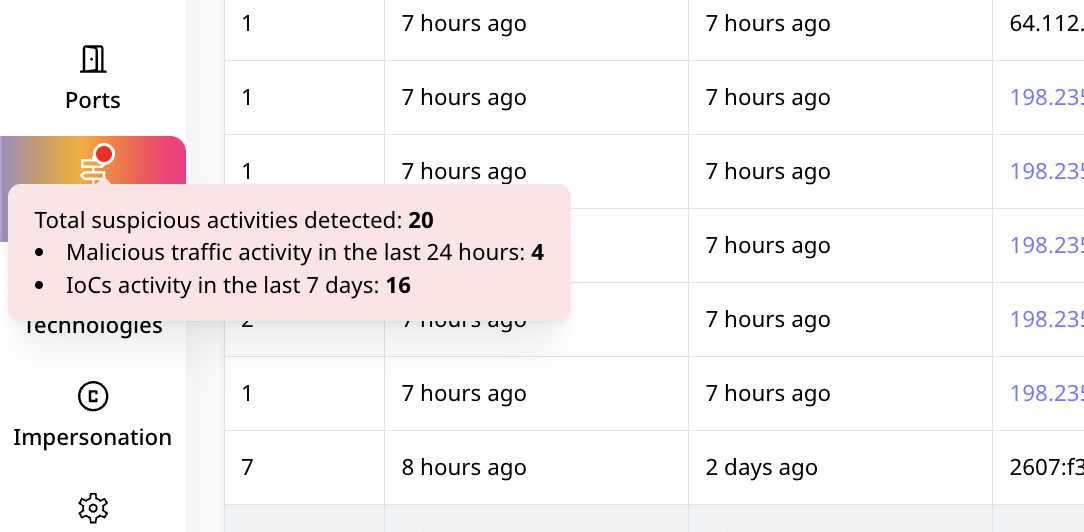
See which assets actively communicate with malicious IPs and prioritize fixing their issues with the help of rich vulnerability intelligence – severity, exploitability, vendor advisories, and other factors.
Respond to Attacks Before They Even Start
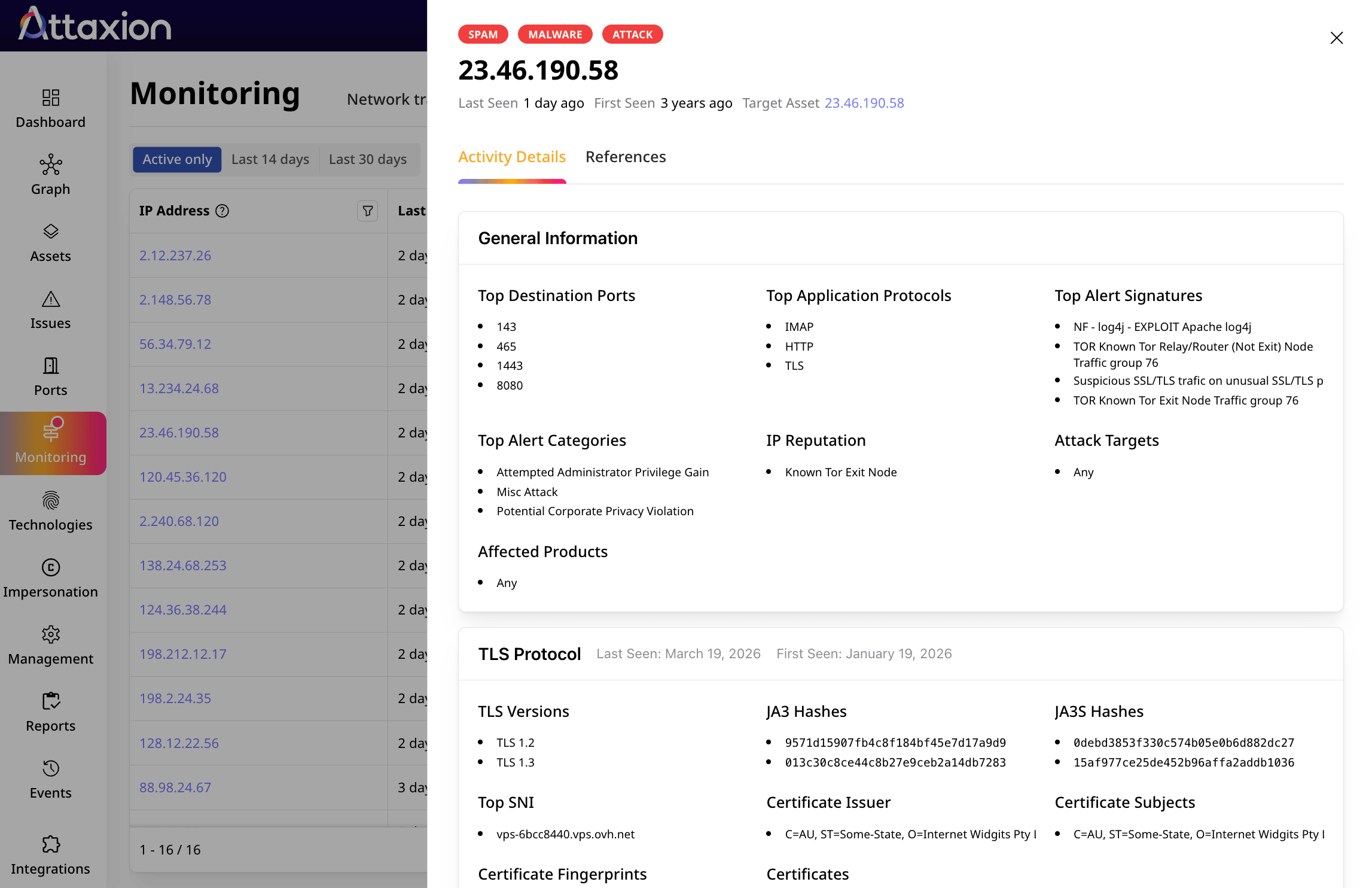
Detect malicious reconnaissance in near real-time and react accordingly. Identify threat actors that are probing your attack surface and mobilize for a proper response.
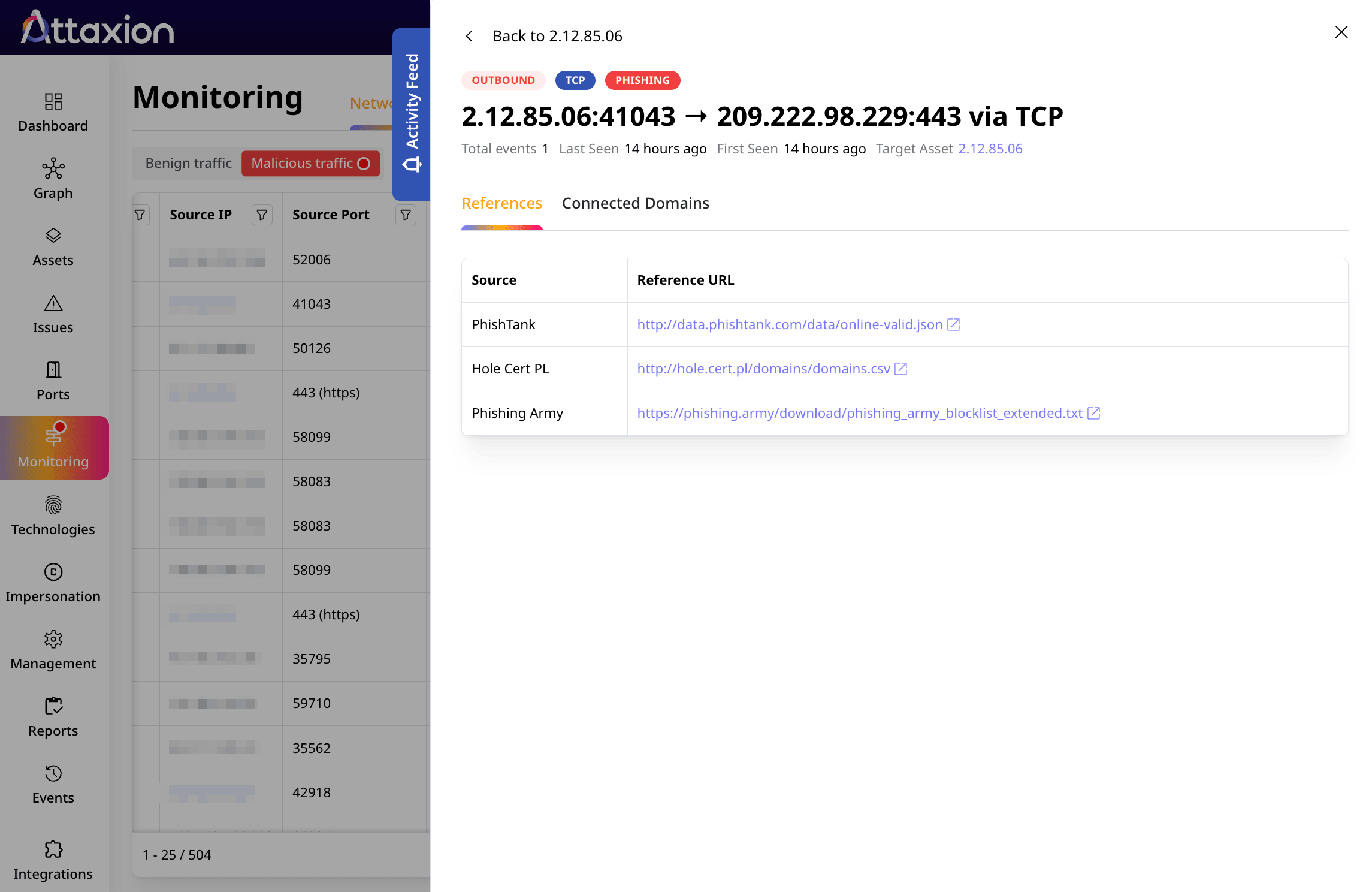
Investigate Threats with Full Context
Attaxion LiveSight brings together asset exposure, real network activity, and threat intelligence in one place — so you can quickly understand what’s happening and why.
What our clients say



The Improved Processes That Attaxion LiveSight Enables
-
With Real-World Activity Data
Understand which exposures actually matter by validating them against real network activity. See which assets and services are truly active, which open ports are receiving traffic that does not align with your security policies, and who is behind those connections. Get alerts when known malicious IPs interact with your infrastructure and focus on the exposures that are not just visible, but actively being threatened.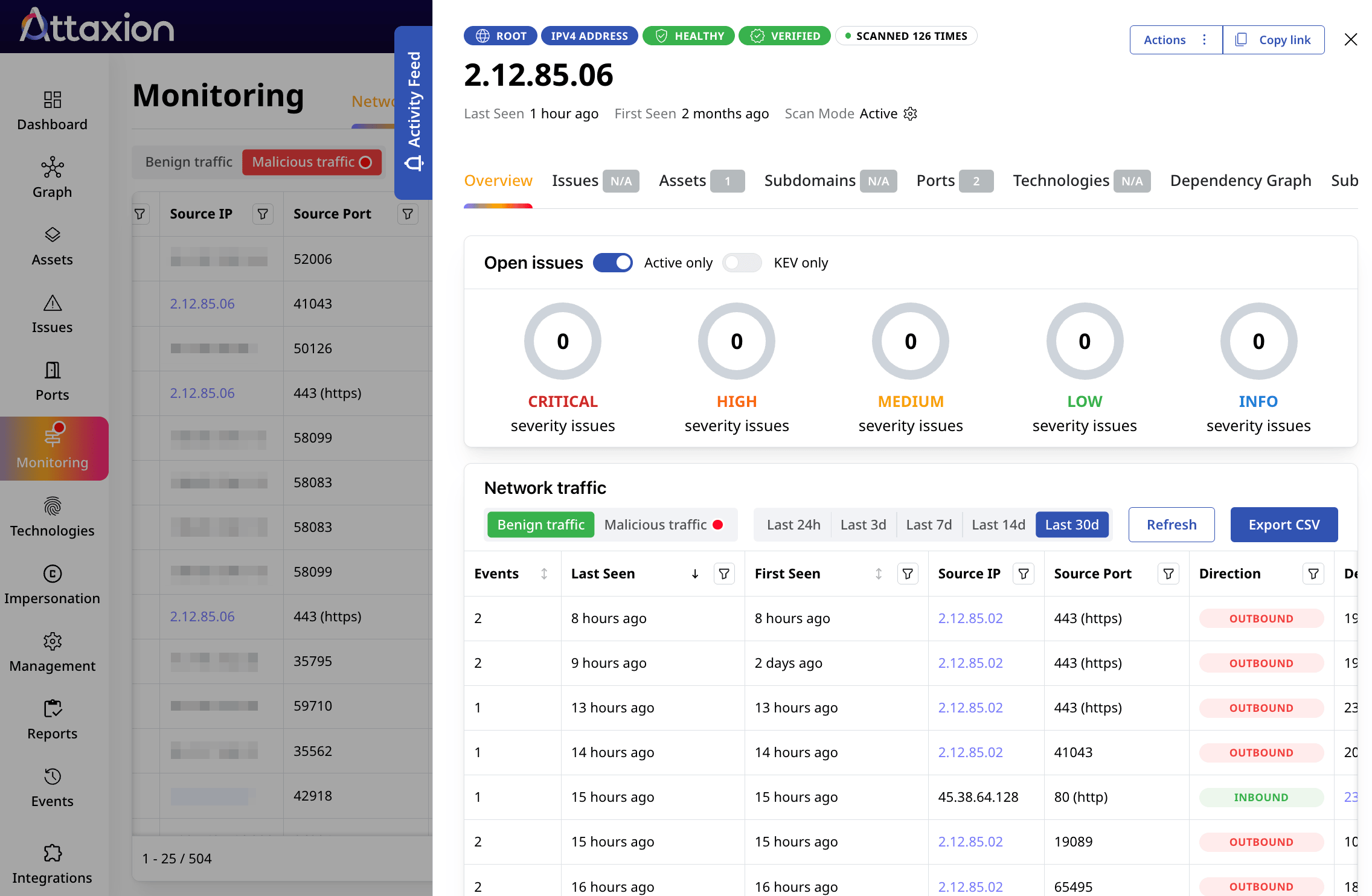
-
With Data That Drives Decisions
Proactively investigate potential threats using real network activity enriched with actionable threat intelligence. Build and validate threat hunting hypotheses based on communication patterns, known malicious IPs, and associated threat actors or attack types. Uncover hidden risks such as compromised assets or overlap with known malicious infrastructure to stay ahead of threats before they turn into serious incidents.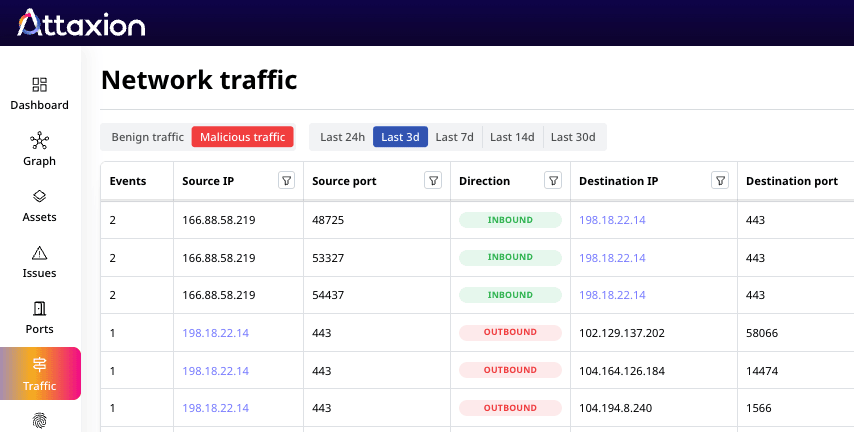
-
With Richer Context and Faster Action
Respond to threats faster with full context on both your exposures and the activity around them. When malicious traffic is detected, instantly see which assets are affected, what vulnerabilities or misconfigurations they have, and how they are being targeted. Quickly scope the incident, prioritize response actions, and take the right mitigation steps without switching between tools.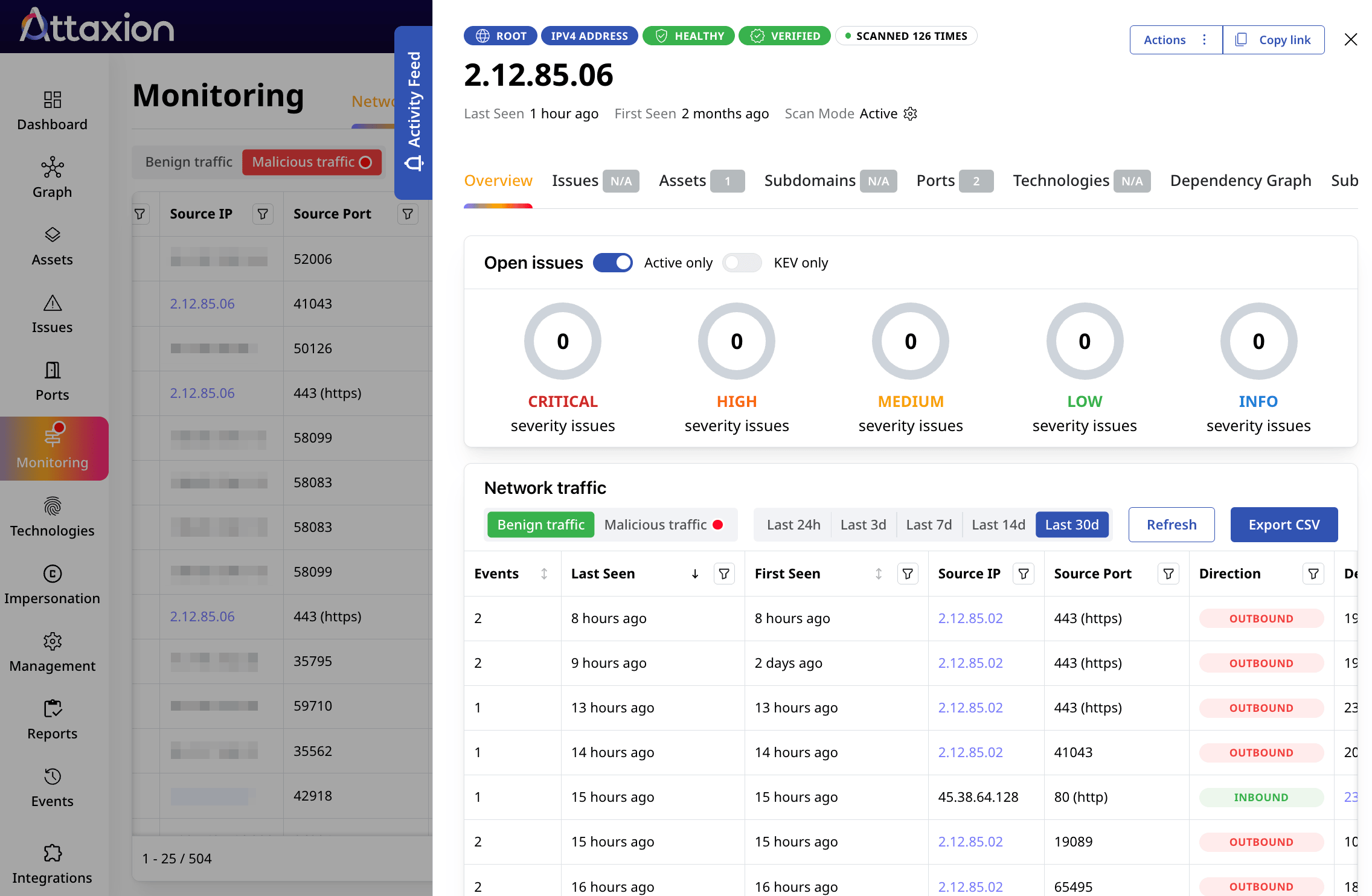
Ready to Try Attaxion LiveSight? Contact Us

10 Critical Attack Surface Metrics to Track
With recent regulatory changes pushing cybersecurity to the boardroom, effective attack surface monitoring and visualization techniques are more cruci[...]

How To Maximize Attack Surface Visibility
One of the major obstacles standing in the way of an effective cybersecurity strategy is getting full attack surface visibility because, as everyone k[...]

M&A Cybersecurity: Managing Cyber Risk for Buyers and Sellers
In high-stakes transactions such as mergers and acquisitions (M&A), speed often takes priority over security. But overlooking cybersecurity can tu[...]