Exposure Management for Lean Security Teams
Exposure Management for Lean Security Teams
Attaxion Core
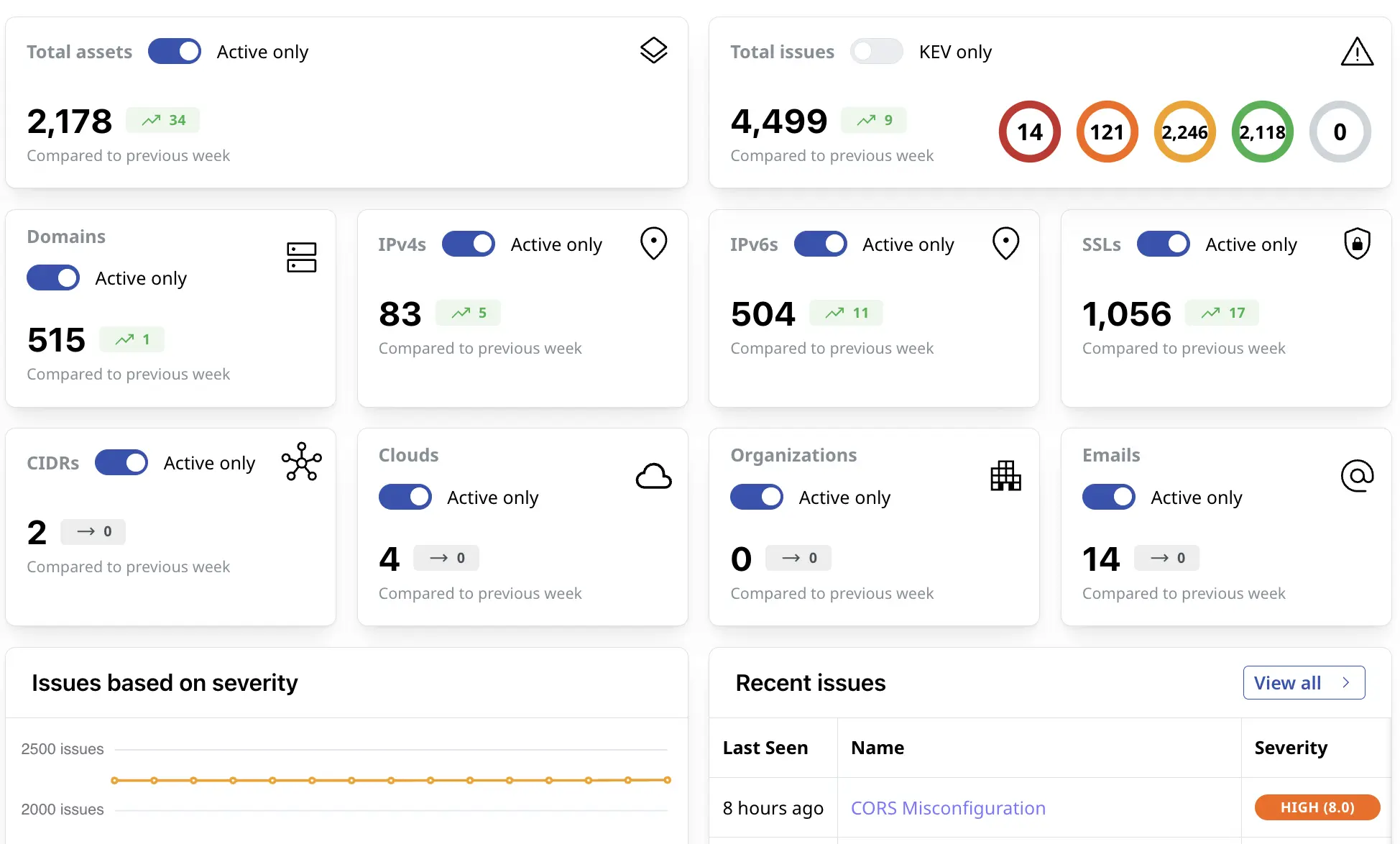
Attaxion Core helps you find ALL your web-facing assets, uncover exposures, prioritize and continuously reduce cyber risks
 Attaxion Core Features
Attaxion Core Features
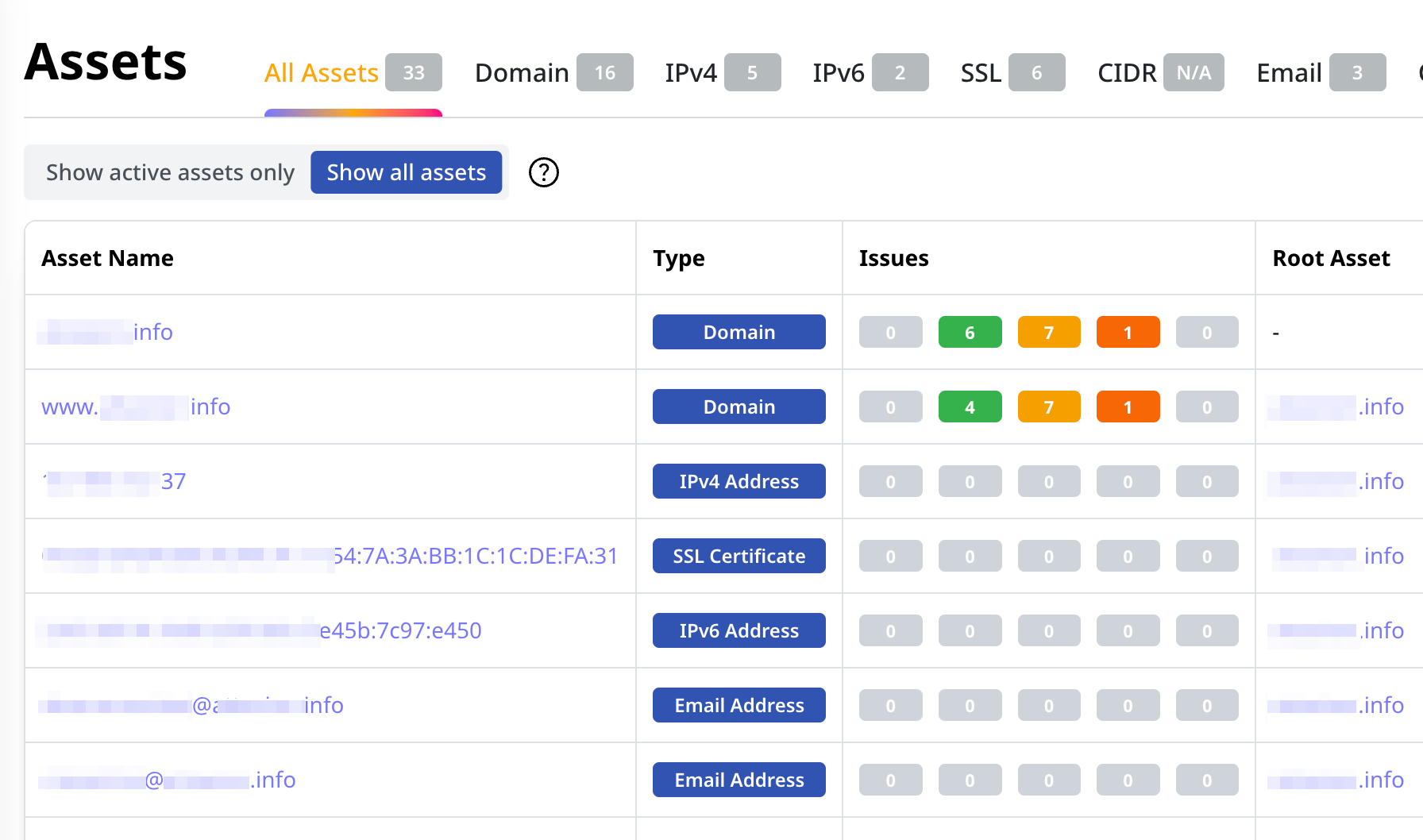
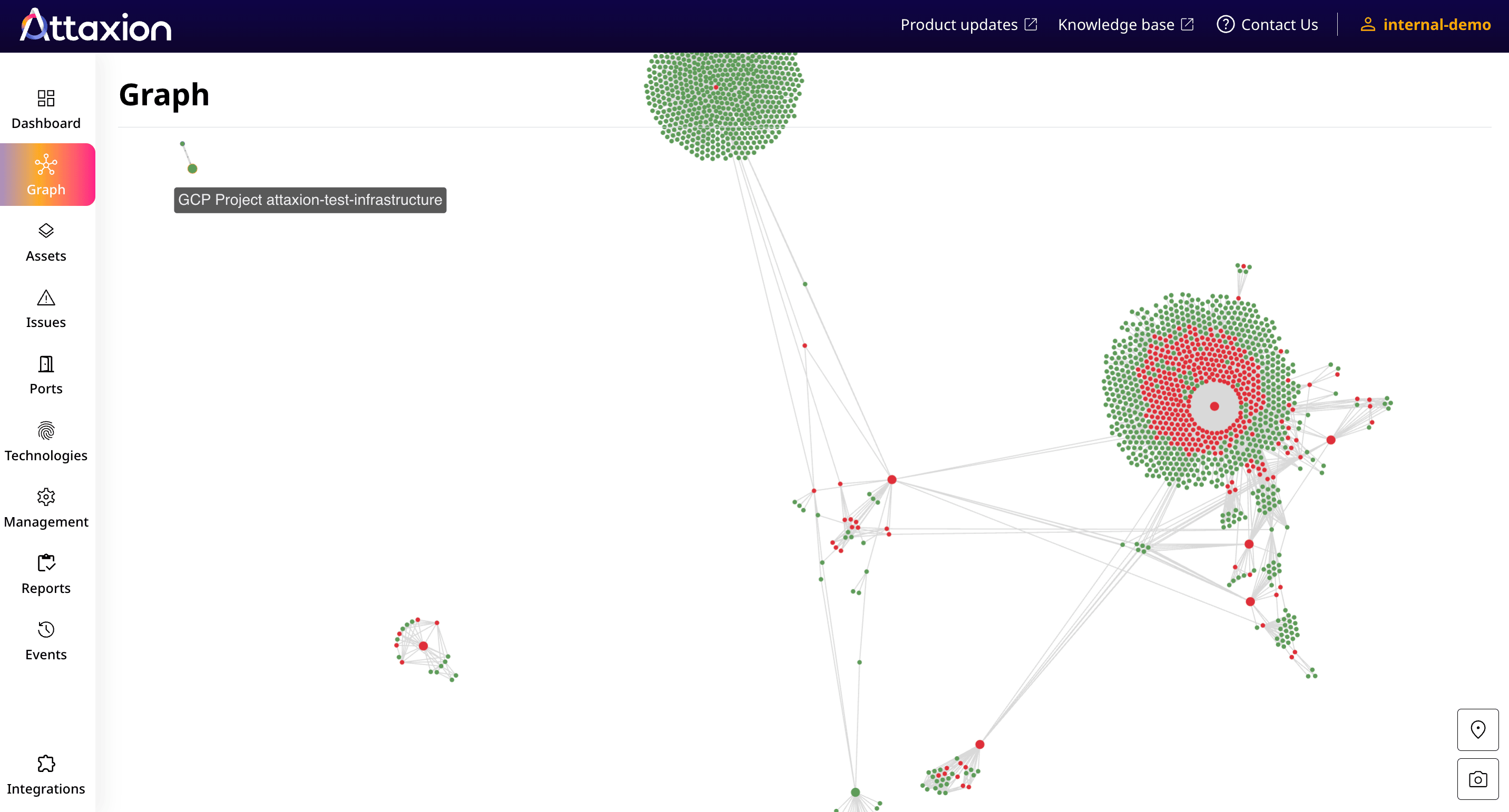
Discovery
Attaxion Core discovers your external assets within hours. Get a real-time inventory of your Internet-facing assets, including their vulnerabilities, connections, and technologies.
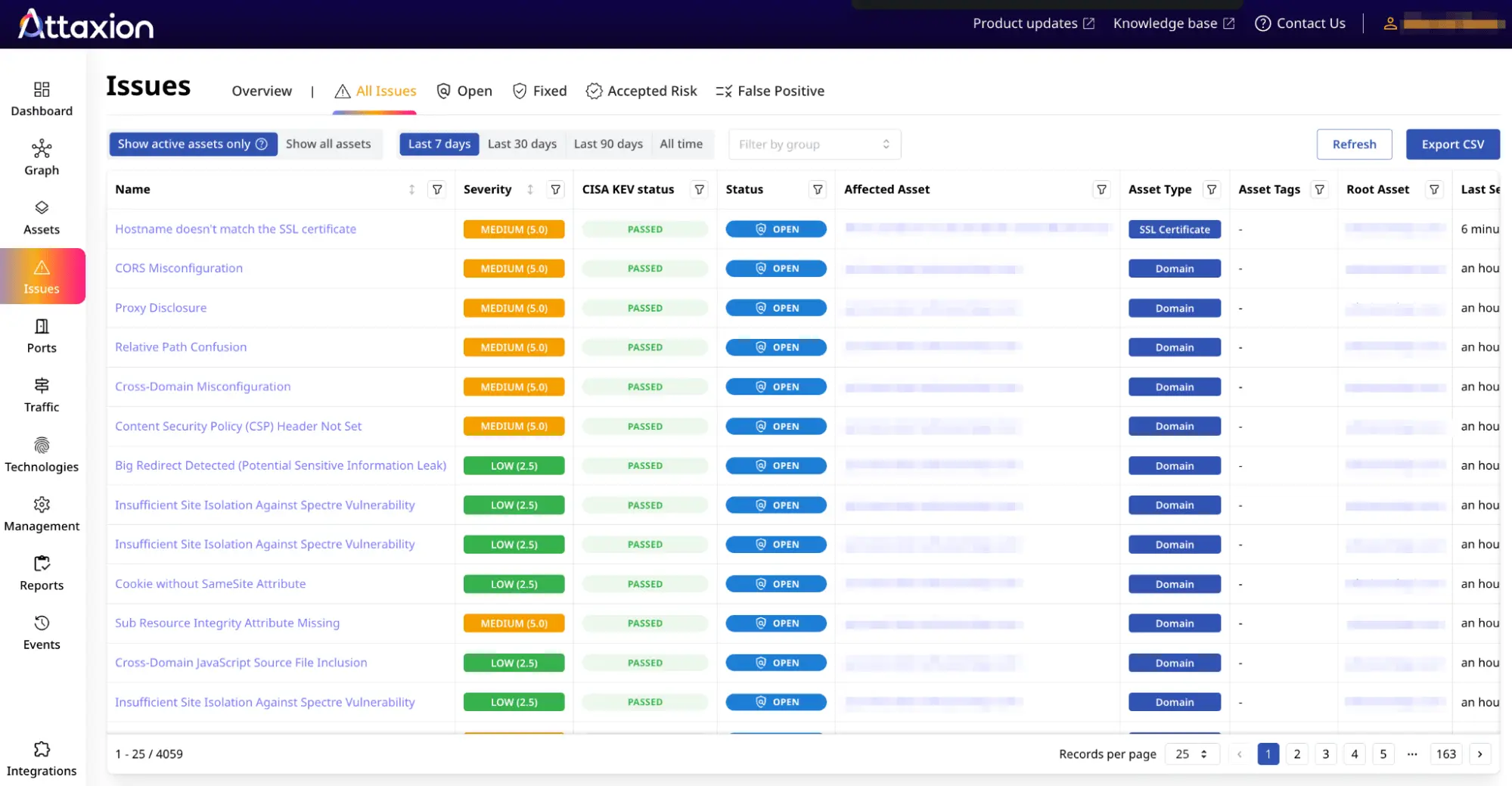
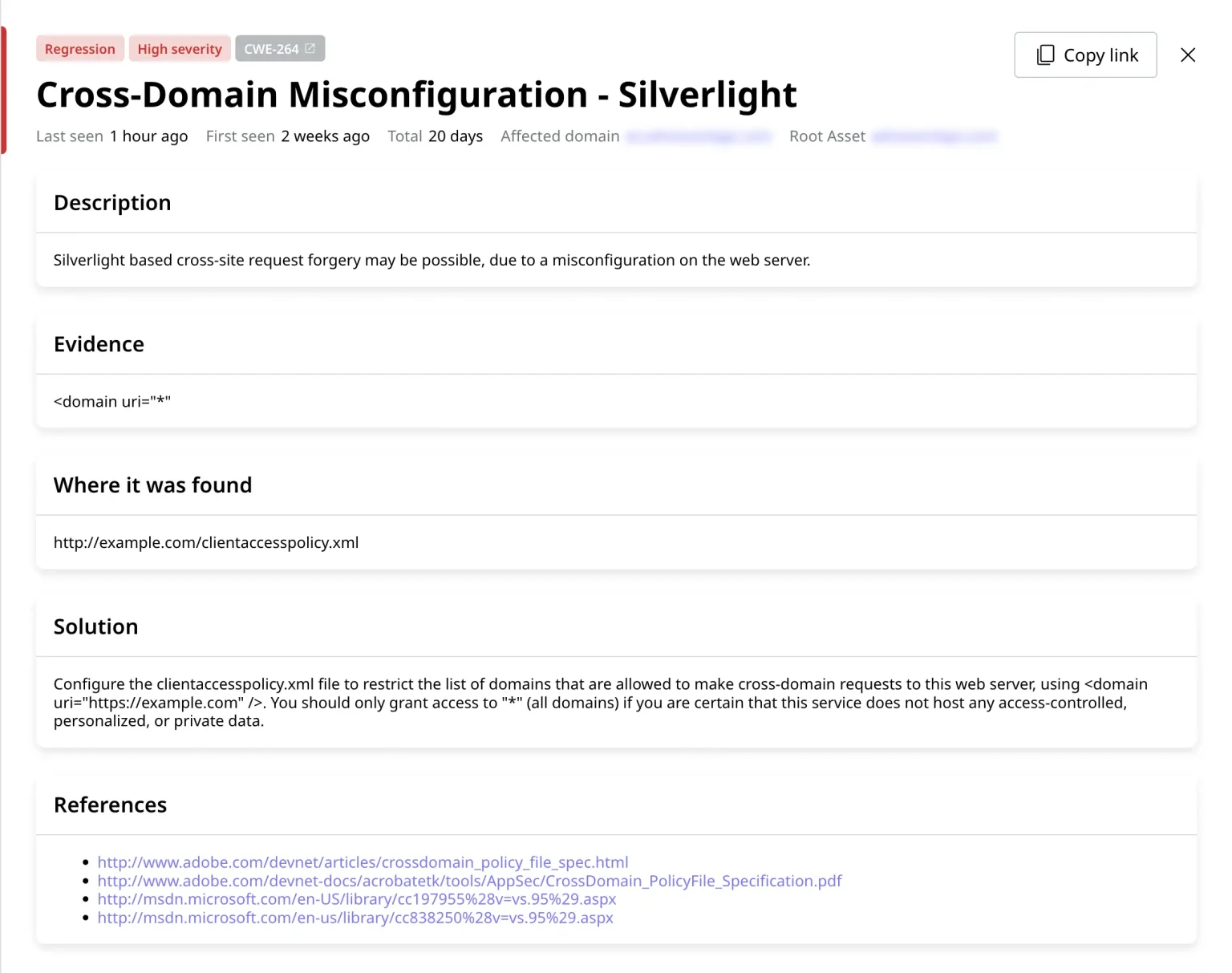
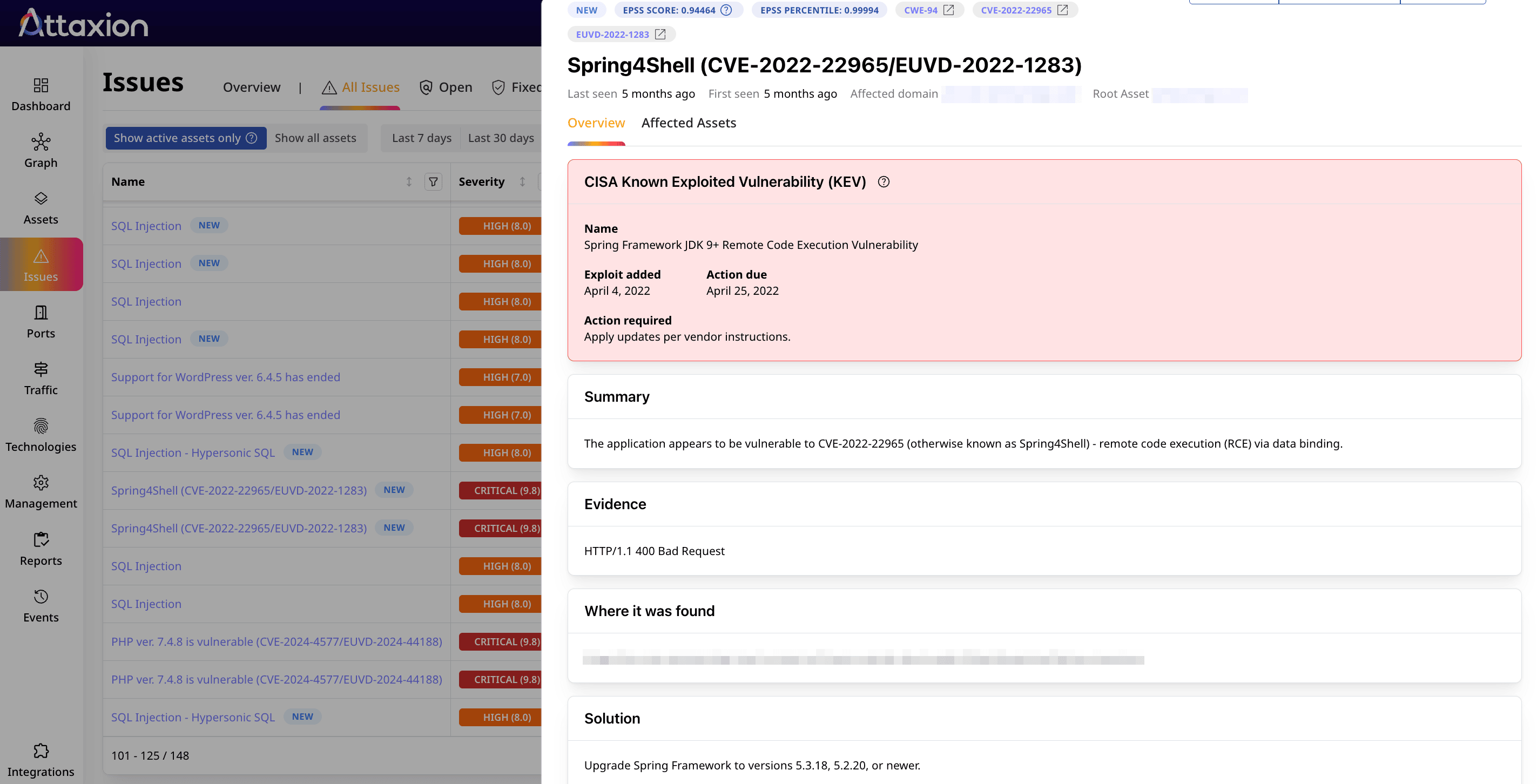
Vulnerability Assessment
Highlight critical and exploitable issues. Prioritize vulnerabilities and misconfigurations based on insights about their severity, exploitability, and affected assets.
Remediation
Simplify risk remediation. Easily assign remediation tasks within your existing workflows and track improvements in your security posture.
Continuous Monitoring
Keep monitoring for new assets and emerging vulnerabilities, and receive customizable alerts. Track remediation progress and overall risk scores.
What our clients say



Why Choose Attaxion Core
-
From CVSS to exploitability, vendor advisories, discovery graphs, and code snippets — Attaxion Core offers rich context for both assets and issues to help you prioritize what really matters.
-
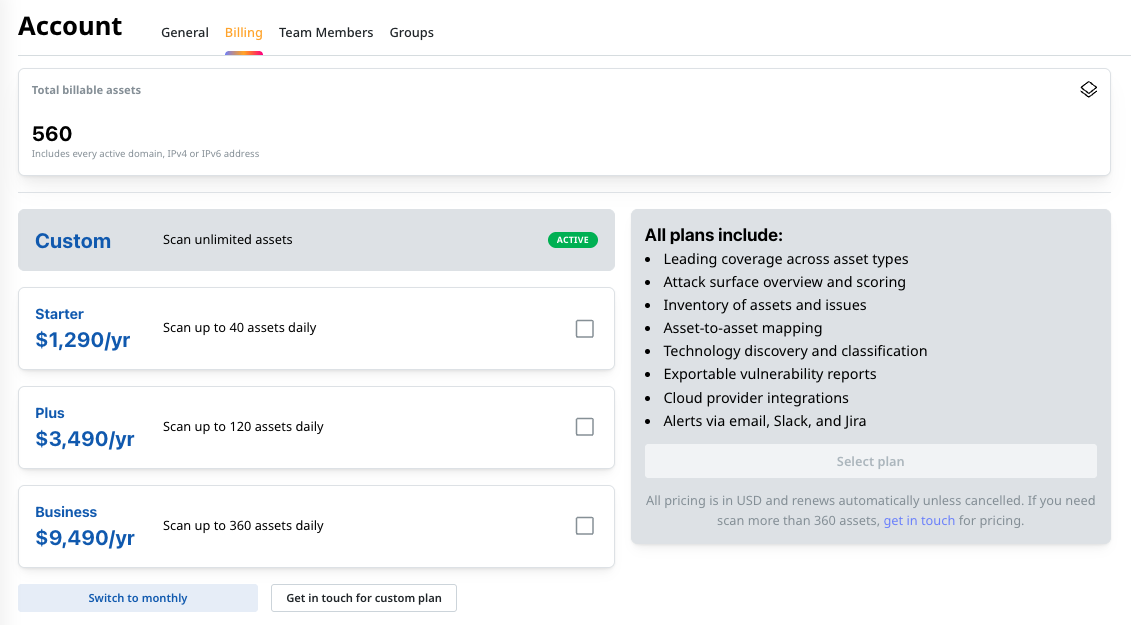
Attaxion Core beats most tools on the market when it comes to pricing per asset. No need to buy special web application scanning licenses or pay extra for asset discovery — Attaxion Core offers it all and scales together with your organization.
-
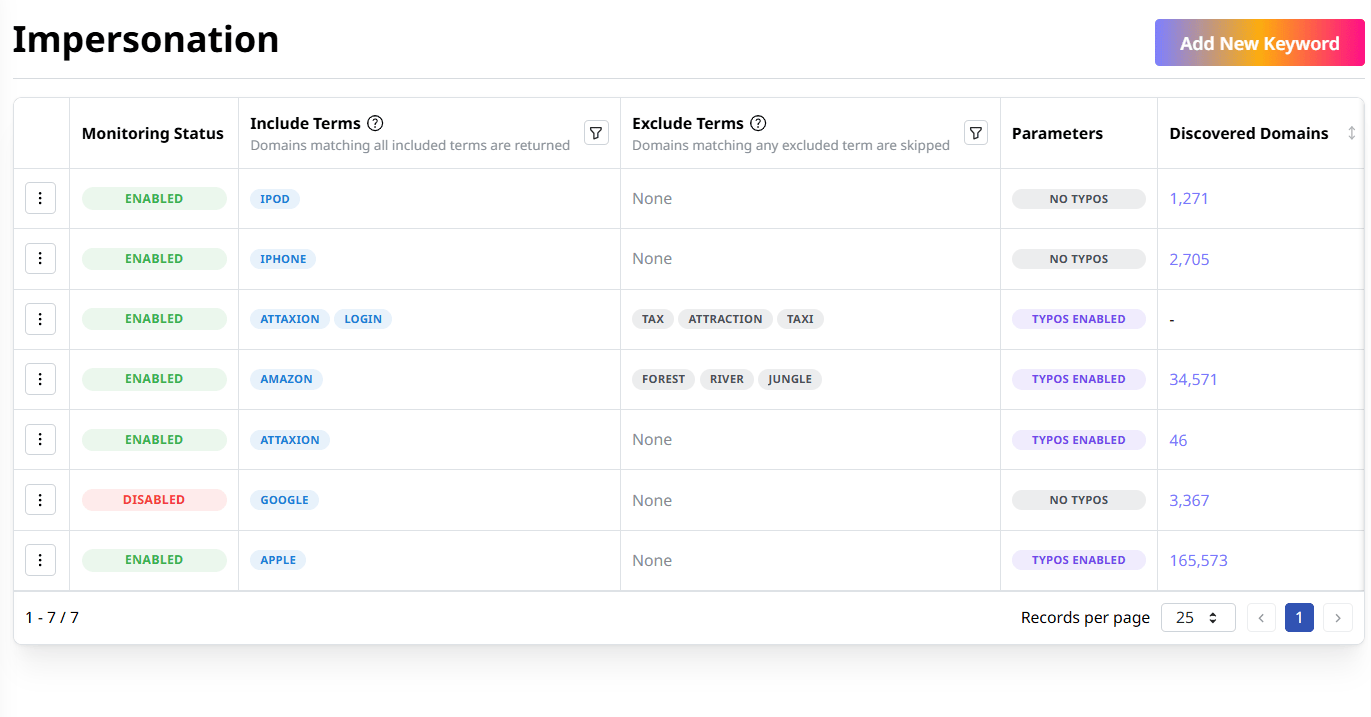
Enhance exposure management with Attaxion Core’s built-in domain brand monitoring, identifying impersonation, phishing, and other domain brand risks from newly registered domains associated with your brand keywords.

10 Critical Attack Surface Metrics to Track
With recent regulatory changes pushing cybersecurity to the boardroom, effective attack surface monitoring and visualization techniques are more cruci[...]

How To Maximize Attack Surface Visibility
One of the major obstacles standing in the way of an effective cybersecurity strategy is getting full attack surface visibility because, as everyone k[...]

M&A Cybersecurity: Managing Cyber Risk for Buyers and Sellers
In high-stakes transactions such as mergers and acquisitions (M&A), speed often takes priority over security. But overlooking cybersecurity can tu[...]