PLATFORM CAPABILITIES
PLATFORM CAPABILITIES
Domain Brand Monitoring
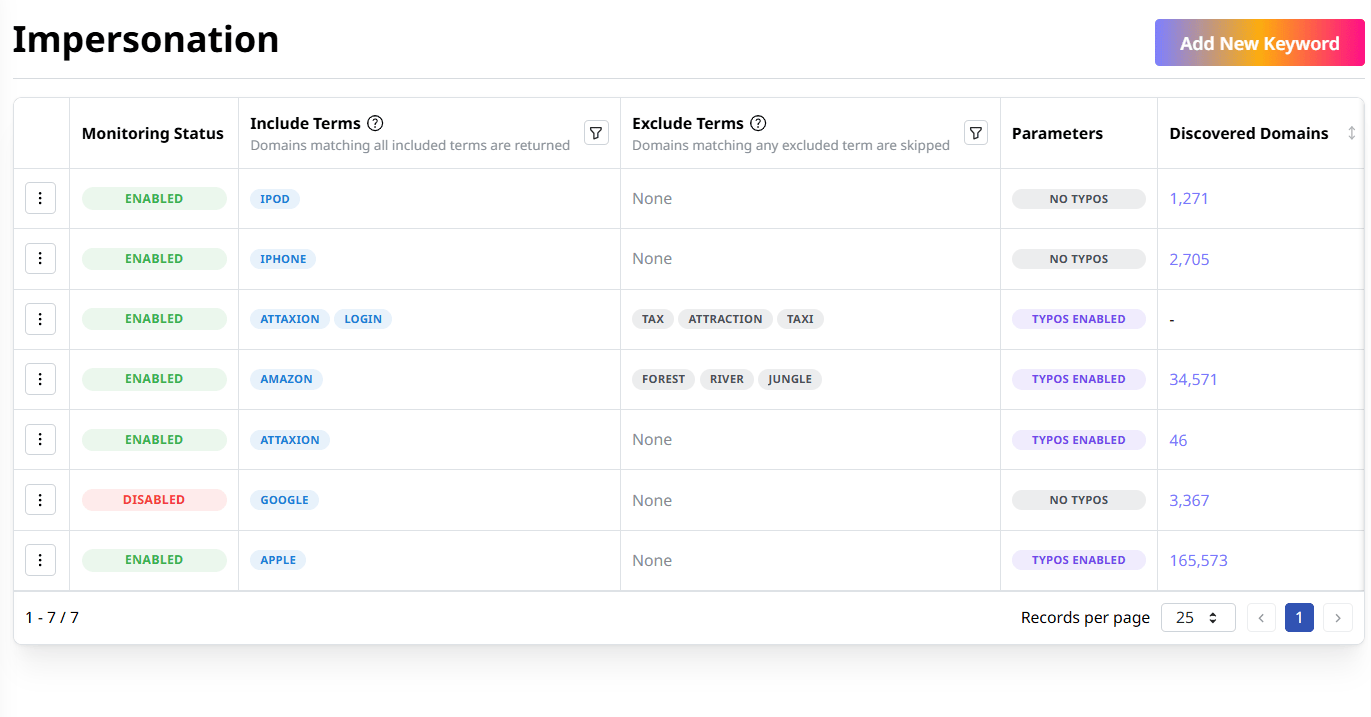
Identify impersonation, phishing, and other domain brand risks with continuous monitoring for new domains associated with your brand keywords.
High-Frequency Domain Monitoring
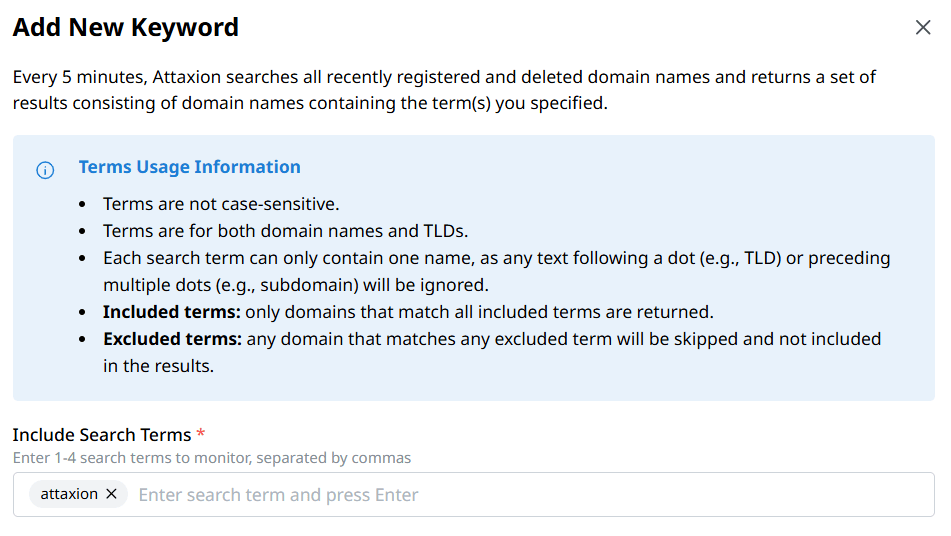
Keep an eye on how your brand names, trademarked products, or the names of top executives are used across the web. Attaxion scans for new domain registrations associated with the brand keywords of your choice every 5 minutes, providing you with near-real-time data on brand threats.
Typosquatting and Look-Alike Domain Detection
Fight against Business Email Compromise (BEC), phishing, and financial fraud — identify domain names with character replacement or common misspellings that mimic your brand.
Precision Filtering
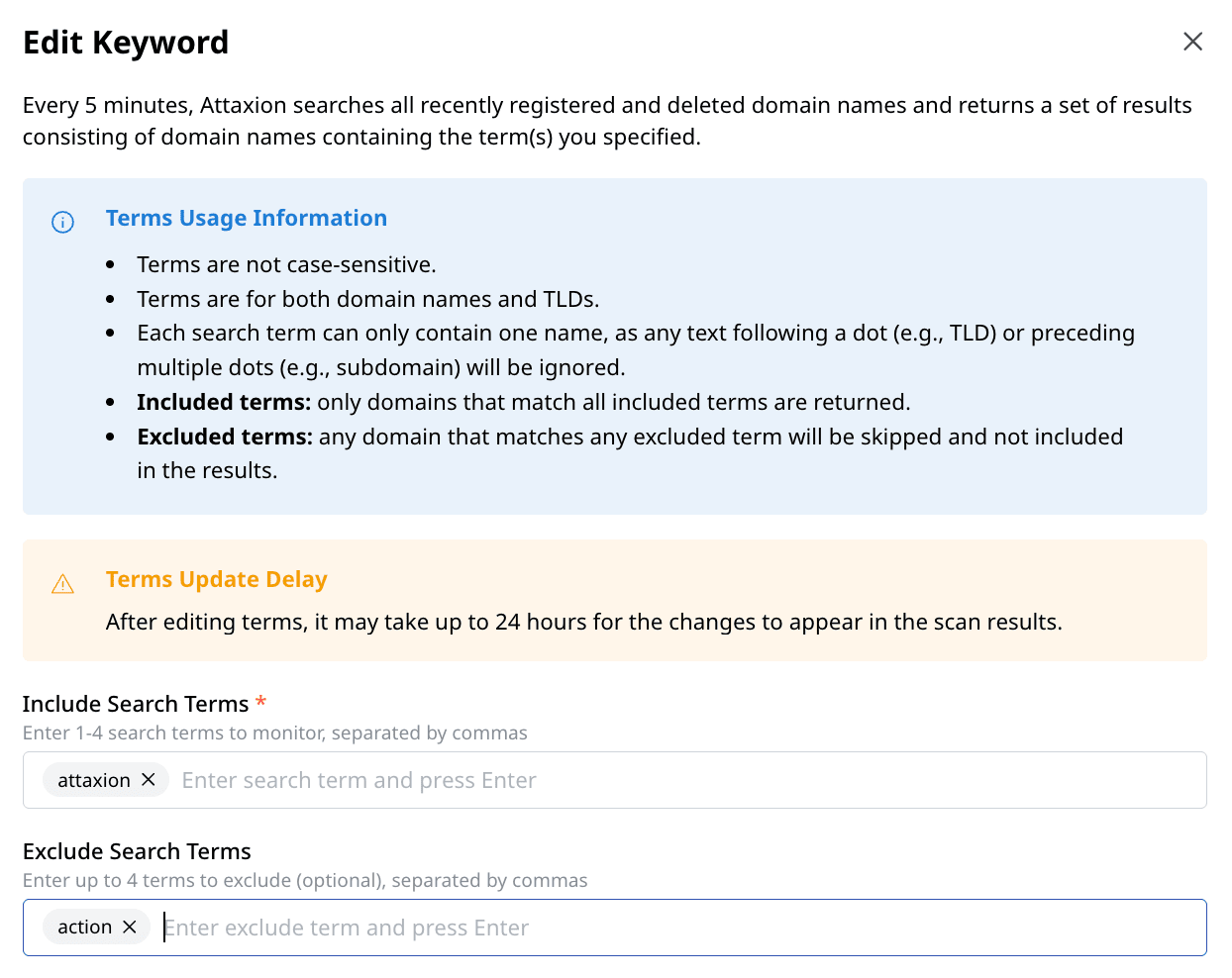
Attaxion's domain brand monitoring feature filters noise by letting you exclude specific keywords to filter out legitimate domains, authorized partners, or common words.
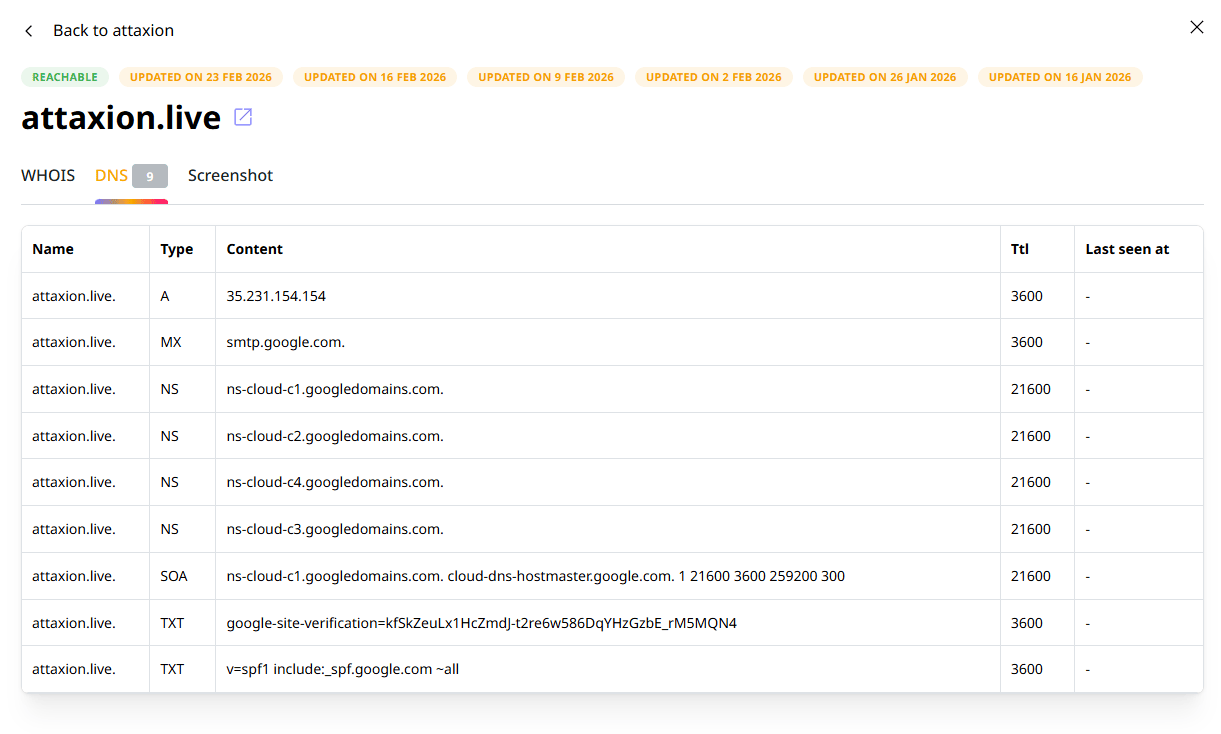
Automated Evidence Collection
Every discovered domain comes with a complete evidence package — domain registration data, DNS records, and website screenshots. Having this technical data lets you quickly validate and facilitate the takedown process.
What security experts say
Why Should You Start Using Attaxion’s Domain Brand Monitoring?
-
Quick Set Up
Simply enter a word or phrase related to your brand, and start tracking threats in minutes.
-
No Limits
Monitor as many keywords as you need without any restrictions.
-
Rich Results
Access wide domain coverage with WHOIS data, DNS records, and web screenshots.
FAQs
Featured Resources

How Are Attack Vectors and Attack Surfaces Related?
Attack vectors and attack surfaces are deeply intertwined cybersecurity concepts. In a nutshell, an attack surface is the sum of all attack vectors in[...]

CWE Vs. CVE Vs. CVSS: What Are the Differences?
When protecting your digital infrastructure from threats, it’s critical to become familiar with security standards like CWE, CVE, and CVSS. These term[...]

How to Find Vulnerabilities in a Website
Website vulnerabilities are exploitable weaknesses that allow attackers to access data without authorization, steal sensitive information, or disrupt[...]